This Companion Guide is the official supplemental textbook for the Networking Essentials course in the Cisco Networking Academy. This sample chapter covers the communication protocols for networks as well as network communication standards. You will also learn what the difference is between the OSI and TCP/IP models.
Objectives
Upon completion of this chapter, you will be able to answer the following questions:
What are network communication protocols?
What are network communication standards?
What is the difference between the OSI and TCP/IP models?
Key Terms
This chapter uses the following key terms. You can find the definitions in the Glossary.
International Organization for Standardization (ISO)
Internet Engineering Task Force (IETF)
Open Systems Interconnection (OSI)
protocol
protocol suite
reference model
Request for Comments (RFC)
Introduction (5.0)
The next day at the hospital, Kishori has a new patient, Srinivas, who has just been admitted to a room. He is from Narayanpet and speaks Telugu. Kishori speaks Marathi. These two Indian languages are very different. Kishori and Srinivas do not speak each other’s native language. However, they do both speak English. Therefore, they decide to communicate using English.
Before beginning to communicate with each other, we establish rules or agreements to govern the conversation. Just like Kishori and Srinivas, we decide what method of communication we should use, and what language we should use. We may also need to confirm that our messages are received. For example, Kishori may have Srinivas sign a document verifying that he has understood Kishori’s care instructions.
Networks also need rules, or protocols, to ensure successful communication. This chapter will cover the communication principles for networks. Let’s get started!
Networking Protocols (5.1)
Before communicating with one another, individuals must use established rules or agreements to govern the conversation. Rules are also required for devices on a network to communicate.
Communication Protocols (5.1.1)
Communication in our daily lives takes many forms and occurs in many environments. We have different expectations depending on whether we are chatting via the Internet or participating in a job interview. Each situation has its corresponding expected behaviors and styles.
Before beginning to communicate with each other, we establish rules or agreements to govern the conversation. These agreements include the following:
Method—What method of communication should we use? (See Figure 5-1.)
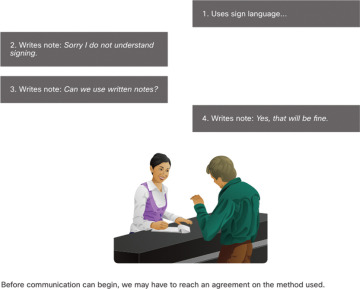
Figure 5-1 Choosing a Method of Communication
Language—What language should we use? (See Figure 5-2.)
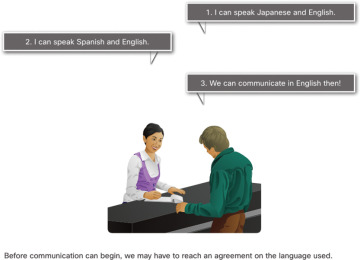
Figure 5-2 Choosing a Language for Communication
Confirmation—Do we need to confirm that our messages are received? (See Figure 5-3.)
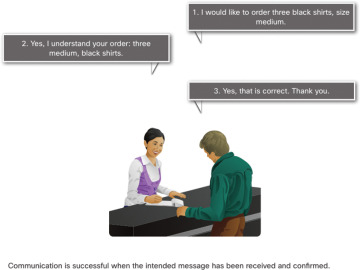
Figure 5-3 Verifying That Communication Was Successful
These rules, or protocols, must be followed for the message to be successfully delivered and understood. Among the protocols that govern successful human communication are these:
An identified sender and receiver
Agreed-upon method of communicating (face-to-face, telephone, letter, photograph)
Common language and grammar
Speed and timing of delivery
Confirmation or acknowledgment requirements
The techniques that are used in network communications share these fundamentals with human conversations.
Think about the commonly accepted protocols for sending text messages to your friends.
Why Protocols Matter (5.1.2)
Just like humans, computers use rules, or protocols, to communicate. Protocols are required for computers to properly communicate across the network. In both a wired and wireless environment, a local network is defined as an area where all hosts must “speak the same language,” which in computer terms means they must “share a common protocol.”
If everyone in the same room spoke a different language, they would not be able to communicate. Likewise, if devices in a local network did not use the same protocols, they would not be able to communicate.
Networking protocols define many aspects of communication over the local network. As shown in Table 5-1, these include message format, message size, timing, encoding, encapsulation, and message pattern.
Table 5-1 Protocol Characteristics
Protocol Characteristic |
Description |
|---|---|
Message format |
When a message is sent, it must use a specific format or structure. Message formats depend on the type of message and the channel that is used to deliver the message. |
Message size |
The rules that govern the size of the pieces communicated across the network are very strict. They can also be different, depending on the channel used. When a long message is sent from one host to another over a network, it may be necessary to break the message into smaller pieces to ensure that the message can be delivered reliably. |
Timing |
Many network communication functions are dependent on timing. Timing determines the speed at which the bits are transmitted across the network. It also affects when an individual host can send data and the total amount of data that can be sent in any one transmission. |
Encoding |
Messages sent across the network are first converted into bits by the sending host. Each bit is encoded into a pattern of sounds, light waves, or electrical pulses depending on the network media over which the bits are transmitted. The destination host receives and decodes the signals to interpret the message. |
Encapsulation |
Each message transmitted on a network must include a header that contains addressing information that identifies the source and destination hosts; otherwise, it cannot be delivered. Encapsulation is the process of adding this information to the pieces of data that make up the message. In addition to addressing, there may be other information in the header that ensures that the message is delivered to the correct application on the destination host. |
Message pattern |
Some messages require an acknowledgment before the next message can be sent. This type of request/response pattern is a common aspect of many networking protocols. However, there are other types of messages that may be simply streamed across the network, without concern as to whether they reach their destination. |
Communication Standards (5.2)
Communication standards are required in all aspects of human communications. For example, when addressing an envelope, there is a standard regarding the placement of the sender’s address, the destination address, and the stamp. Network communication also requires standards to ensure that all the devices in the network are using the same rules to send and receive information.
Video—Devices in a Bubble (5.2.1)
Refer to the online course to view this video.
The Internet and Standards (5.2.2)
With the increasing number of new devices and technologies coming online, how is it possible to manage all the changes and still reliably deliver services such as email? The answer is Internet standards.
A standard is a set of rules that determines how something must be done. Networking and Internet standards ensure that all devices connecting to the network implement the same set of rules or protocols in the same manner. Using standards enables different types of devices to send information to each other over the Internet. For example, the way in which an email is formatted, forwarded, and received by all devices is done according to a standard. If one person sends an email via a personal computer, another person can use a mobile phone to receive and read the email as long as the mobile phone uses the same standards as the personal computer.
Network Standards Organizations (5.2.3)
An Internet standard is the end result of a comprehensive cycle of discussion, problem solving, and testing. These different standards are developed, published, and maintained by a variety of organizations. When a new standard is proposed, each stage of the development and approval process is recorded in a numbered Request for Comments (RFC) document so that the evolution of the standard is tracked. RFCs for Internet standards are published and managed by the Internet Engineering Task Force (IETF).
The logos of IETF and other standards organizations that support the Internet are shown in Figure 5-4.

Figure 5-4 Internet Standards Organizations
Network Communication Models (5.3)
Network communication models help us understand the various components and protocols used in network communications. These models help us see the function of each protocol and their relationship to other protocols.
Video—Network Protocols (5.3.1)
Refer to the online course to view this video.
Video—The Protocol Stack (5.3.2)
Refer to the online course to view this video.
The TCP/IP Model (5.3.3)
Layered models help us visualize how the various protocols work together to enable network communications. A layered model depicts the operation of the protocols occurring within each layer, as well as the interaction with the layers above and below it. The layered model has many benefits:
Assists in protocol design, because protocols that operate at a specific layer have defined information that they act upon and a defined interface to the layers above and below.
Fosters competition because products from different vendors can work together.
Enables technology changes to occur at one level without affecting the other levels.
Provides a common language to describe networking functions and capabilities.
The first layered model for internetwork communications was created in the early 1970s and is referred to as the Internet model. It defines four categories of functions that must occur for communications to be successful. The suite of TCP/IP protocols that are used for Internet communications follows the structure of this model, as shown in Table 5-2. Because of this, the Internet model is commonly referred to as the TCP/IP model.
Table 5-2 The Layers of the TCP/IP Model
TCP/IP Model Layer |
Description |
|---|---|
Application |
Represents data to the user, plus encoding and dialog control. |
Transport |
Supports communication between various devices across diverse networks. |
Internet |
Determines the best path through the network. |
Network Access |
Controls the hardware devices and media that make up the network. |
The OSI Reference Model (5.3.4)
Two basic types of models are used to describe the functions that must occur for network communications to be successful:
Protocol model—This type of model closely matches the structure of a particular protocol suite. A protocol suite includes the set of related protocols that typically provide all the functionality required for people to communicate with the data network. The TCP/IP model is a protocol model because it describes the functions that occur at each layer of protocols within the TCP/IP suite.
Reference model—This type of model describes the functions that must be completed at a particular layer but does not specify exactly how a function should be accomplished. A reference model is not intended to provide a sufficient level of detail to define precisely how each protocol should work at each layer. The primary purpose of a reference model is to aid in clearer understanding of the functions and processes necessary for network communications.
The most widely known internetwork reference model was created by the Open Systems Interconnection (OSI) project at the International Organization for Standardization (ISO). It is used for data network design, operation specifications, and troubleshooting. This model is commonly referred to as the OSI model. The OSI layers are described in Table 5-3.
Table 5-3 The Layers of the OSI Model
OSI Model Layer |
Description |
|---|---|
7—Application |
The application layer contains protocols used for process-to-process communications. |
6—Presentation |
The presentation layer provides for common representation of the data transferred between application layer services. |
5—Session |
The session layer provides services to the presentation layer to organize its dialogue and to manage data exchange. |
4—Transport |
The transport layer defines services to segment, transfer, and reassemble the data for individual communications between the end devices. |
3—Network |
The network layer provides services to exchange the individual pieces of data over the network between identified end devices. |
2—Data link |
The data link layer protocols describe methods for exchanging data frames between devices over a common media. |
1—Physical |
The physical layer protocols describe the mechanical, electrical, functional, and procedural means to activate, maintain, and de-activate physical connections for a bit transmission to and from a network device. |
OSI Model and TCP/IP Model Comparison (5.3.5)
Because TCP/IP is the protocol suite in use for Internet communications, why do you need to learn the OSI model as well?
The TCP/IP model is a method of visualizing the interactions of the various protocols that make up the TCP/IP protocol suite. It does not describe general functions that are necessary for all networking communications. It describes the networking functions specific to those protocols in use in the TCP/IP protocol suite. For example, at the network access layer, the TCP/IP protocol suite does not specify which protocols to use when transmitting over a physical medium, nor the method of encoding the signals for transmission. OSI Layers 1 and 2 discuss the necessary procedures to access the media and the physical means to send data over a network.
The protocols that make up the TCP/IP protocol suite can be described in terms of the OSI reference model. The functions that occur at the Internet layer in the TCP/IP model are contained in the network layer of the OSI model, as shown in Figure 5-5. The transport layer functionality is the same between both models. However, the network access layer and the application layer of the TCP/IP model are further divided in the OSI model to describe discrete functions that must occur at these layers.
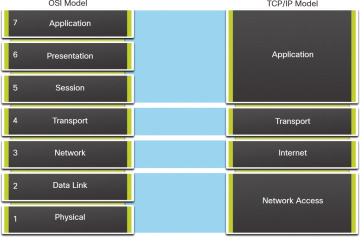
Figure 5-5 The OSI and TCP/IP Models
The key similarities are in the transport and network layers; however, the two models differ in how they relate to the layers above and below each layer:
OSI Layer 3, the network layer, maps directly to the TCP/IP Internet layer. This layer is used to describe protocols that address and route messages through an internetwork.
OSI Layer 4, the transport layer, maps directly to the TCP/IP transport layer. This layer describes general services and functions that provide ordered and reliable delivery of data between source and destination hosts.
The TCP/IP application layer includes several protocols that provide specific functionality to a variety of end-user applications. The OSI model Layers 5, 6, and 7 are used as references for application software developers and vendors to produce applications that operate on networks.
Both the TCP/IP and OSI models are commonly used when referring to protocols at various layers. Because the OSI model separates the data link layer from the physical layer, it is commonly used when referring to these lower layers.
Communication Principles Summary (5.4)
The following is a summary of each topic in the chapter and some questions for your reflection.
What Did I Learn in This Chapter? (5.4.1)
Communication Protocol—Protocols are required for computers to properly communicate across the network. Protocols define the following aspects of communication over the local network:
 Message format—When a message is sent, it must use a specific format or structure.
Message format—When a message is sent, it must use a specific format or structure. Message size—The rules that govern the size of the pieces communicated across the network are very strict. They can also be different, depending on the channel used.
Message size—The rules that govern the size of the pieces communicated across the network are very strict. They can also be different, depending on the channel used. Timing—Timing determines the speed at which the bits are transmitted across the network. It also affects when an individual host can send data and the total amount of data that can be sent in any one transmission.
Timing—Timing determines the speed at which the bits are transmitted across the network. It also affects when an individual host can send data and the total amount of data that can be sent in any one transmission. Encoding—Messages sent across the network are first converted into bits by the sending host. Each bit is encoded into a pattern of sounds, light waves, or electrical pulses depending on the network media over which the bits are transmitted.
Encoding—Messages sent across the network are first converted into bits by the sending host. Each bit is encoded into a pattern of sounds, light waves, or electrical pulses depending on the network media over which the bits are transmitted. Encapsulation—Each message transmitted on a network must include a header that contains addressing information that identifies the source and destination hosts. Encapsulation is the process of adding this information to the pieces of data that make up the message.
Encapsulation—Each message transmitted on a network must include a header that contains addressing information that identifies the source and destination hosts. Encapsulation is the process of adding this information to the pieces of data that make up the message. Message pattern—Some messages require an acknowledgment before the next message can be sent. This type of request/response pattern is a common aspect of many networking protocols. However, other types of messages may be simply streamed across the network, without concern as to whether they reach their destination.
Message pattern—Some messages require an acknowledgment before the next message can be sent. This type of request/response pattern is a common aspect of many networking protocols. However, other types of messages may be simply streamed across the network, without concern as to whether they reach their destination.
Communication Standards—Topologies allow us to see the networking using representation of end devices and intermediary devices. How does a device see a network? Think of a device in a bubble. The only thing a device sees is its own addressing information. How does the device know it is on the same network as another device? The answer is network protocols. Most network communications are broken up into smaller data units, or packets.
A standard is a set of rules that determines how something must be done. Networking and Internet standards ensure that all devices connecting to the network implement the same set of rules or protocols in the same manner. Using standards enables different types of devices to send information to each other over the Internet.
An Internet standard is the end result of a comprehensive cycle of discussion, problem solving, and testing. Internet standards are developed, published, and maintained by a variety of organizations. When a new standard is proposed, each stage of the development and approval process is recorded in a numbered RFC document so that the evolution of the standard is tracked. RFCs for Internet standards are published and managed by the IETF.
Network Communication Models—Protocols are the rules that govern communications. Successful communication between hosts requires interaction between a number of protocols. Protocols include HTTP, TCP, IP, and Ethernet. These protocols are implemented in software and hardware that are installed on each host and networking device.
The interaction between the different protocols on a device can be illustrated as a protocol stack. A stack illustrates the protocols as a layered hierarchy, with each higher-level protocol depending on the services of the protocols shown in the lower levels. The separation of functions enables each layer in the stack to operate independently of others.
The suite of TCP/IP protocols that are used for Internet communications follows the structure of this model:
 Application—Represents data to the user, plus encoding and dialog control
Application—Represents data to the user, plus encoding and dialog control Transport—Supports communication between various devices across diverse networks
Transport—Supports communication between various devices across diverse networks Internet—Determines the best path through the network
Internet—Determines the best path through the network Network Access—Controls the hardware devices and media that make up the network
Network Access—Controls the hardware devices and media that make up the network
A reference model describes the functions that must be completed at a particular layer but does not specify exactly how a function should be accomplished. The primary purpose of a reference model is to aid in clearer understanding of the functions and processes necessary for network communications.
The most widely known internetwork reference model was created by the OSI project at the ISO. It is used for data network design, operation specifications, and troubleshooting. This model is commonly referred to as the OSI model.
The layers in the OSI model are as follows:
 7—Application—Contains protocols used for process-to-process communications
7—Application—Contains protocols used for process-to-process communications 6—Presentation—Provides for common representation of the data transferred between application layer services
6—Presentation—Provides for common representation of the data transferred between application layer services 5—Session—Provides services to the presentation layer to organize its dialogue and to manage data exchange
5—Session—Provides services to the presentation layer to organize its dialogue and to manage data exchange 4—Transport—Defines services to segment, transfer, and reassemble the data for individual communications between the end devices
4—Transport—Defines services to segment, transfer, and reassemble the data for individual communications between the end devices 3—Network—Provides services to exchange the individual pieces of data over the network between identified end devices
3—Network—Provides services to exchange the individual pieces of data over the network between identified end devices 2—Data link—Includes protocols that describe methods for exchanging data frames between devices over a common media
2—Data link—Includes protocols that describe methods for exchanging data frames between devices over a common media 1—Physical—Includes protocols that describe the mechanical, electrical, functional, and procedural means to activate, maintain, and de-activate physical connections for a bit transmission to and from a network device
1—Physical—Includes protocols that describe the mechanical, electrical, functional, and procedural means to activate, maintain, and de-activate physical connections for a bit transmission to and from a network device
Reflection Questions (5.4.2)
Recall that Kishori and Srinivas had to determine a common language. Do you have any friends or relatives whose first language is different than yours? Do you know anyone who uses sign language? How would you communicate with them if you did not know sign language? Did you realize before reading this chapter that you were using a protocol (using a shared language or communicating in writing) to interact with family and friends?
Check Your Understanding Questions
Complete all the review questions listed here to test your understanding of the topics and concepts in this chapter. Appendix A, “Answers to ‘Check Your Understanding’ Questions,” lists the answers.
What is the purpose of the OSI physical layer?
To control access to media
To transmit bits across the local media
To perform error detection on received frames
To exchange frames between nodes over physical network media
Which statement is correct about network protocols?
They define the type of hardware that is used and how it is mounted in racks.
They define how messages are exchanged between the source and the destination.
They all function in the network access layer of TCP/IP.
They are required only for exchange of messages between devices on remote networks.
What networking term describes a particular set of rules at one layer that governs communication at that layer?
Duplex
Encapsulation
Error checking
Protocol
Which layer of the OSI model defines services to segment and reassemble data for individual communications between end devices?
Application
Presentation
Session
Transport
Network
What is the purpose of protocols in data communications?
To specify the bandwidth of the channel or medium for each type of communication
To specify the device operating systems that will support the communication
To provide the rules required for a specific type of communication to occur
To dictate the content of the message sent during communication
Which term refers to a formalized protocol, usually approved by an accepted authority or organization, which can then be implemented by different vendors?
Standard
Protocol
Model
Domain
Which three layers of the OSI model make up the application layer of the TCP/IP model? (Choose three.)
Data link
Network
Transport
Session
Presentation
Application
Which organization publishes and manages the Request for Comments (RFC) documents?
IEEE
ISO
IETF
TIA/EIA
Which two OSI model layers have the same functionality as a single layer of the TCP/IP model? (Choose two.)
Data link
Network
Physical
Session
Transport