Broadband solutions provide teleworkers with high-speed connection options to business locations and to the Internet. In this sample chapter from Connecting Networks v6 Companion Guide, identify branch connection options for small to medium-sized businesses, basic configuration for a PPPoE connection on a client router, and more.
Objectives
Upon completion of this chapter, you will be able to answer the following questions:
What are the remote-access broadband connection options for small- to medium-sized businesses?
What is the appropriate broadband connection for a given network requirement?
What is PPPOE and how does it operate?
What is the basic configuration for a PPPoE connection on a client router?
What are the benefits of VPN technology?
What are the features of site-to-site and remote-access VPNs?
What is the purpose and what are the benefits of GRE tunnels?
How do you troubleshoot a site-to-site GRE tunnel?
What are the basic BGP features?
What are the basic BGP design considerations?
How do you configure an eBGP branch connection?
Key Terms
This chapter uses the following key terms. You can find the definitions in the Glossary.
PPP over Ethernet (PPPoE)
Internet Protocol Security (IPsec)
Border Gateway Protocol (BGP)
radio frequency (RF)
hybrid fiber-coaxial (HFC)
Data over Cable Service Interface Specification (DOCSIS)
antenna site
transportation network
distribution network
central office (CO)
amplifier
subscriber drop
node
downstream
upstream
asymmetric DSL (ADSL)
symmetric DSL (SDSL)
DSL transceiver
DSL micro filter
Cellular/mobile
dialer interface
maximum transmission unit (MTU)
maximum segment size (MSS)
VPN gateway
telecommuters
VPN client software
Cisco AnyConnect Secure Mobility Client
Dynamic Multipoint VPN (DMVPN)
Next Hop Resolution Protocol (NHRP)
Next Hop Server (NHS)
Next Hop Clients (NHCs)
spoke-to-spoke
Multipoint Generic Routing Encapsulation (mGRE)
Passenger protocol
Carrier protocol
Transport protocol
Secure Sockets Layer (SSL)
AS number (ASN)
path vector routing protocol
external BGP (eBGP)
internal BGP (iBGP)
multihomed
single-homed
BGP peers
Network Address Translation (NAT)
Introduction (3.0)
Broadband solutions provide teleworkers with high-speed connection options to business locations and to the Internet. Small branch offices can also connect using these same technologies. This chapter covers commonly used broadband solutions, such as cable, DSL, and wireless.
ISPs value the Point-to-Point Protocol (PPP) because of the authentication, accounting, and link management features. Customers appreciate the ease and availability of the Ethernet connection. Ethernet links do not natively support PPP. A solution to this problem was created: PPP over Ethernet (PPPoE). This chapter covers the implementation of PPPoE.
Security is a concern when using the public Internet to conduct business. Virtual private networks (VPNs) are used to improve the security of data across the Internet. A VPN is used to create a private communication channel (also called a tunnel) over a public network. Data can be secured by using encryption in this tunnel through the Internet and by using authentication to protect data from unauthorized access. VPN technology provides security options for data running over these connections. This chapter describes some basic VPN implementations.
Generic Routing Encapsulation (GRE) is a tunneling protocol developed by Cisco that can encapsulate a wide variety of protocol packet types inside IP tunnels. GRE creates a virtual point-to-point link to Cisco routers at remote points, over an IP internetwork. The chapter covers the basic GRE implementation.
The Border Gateway Protocol (BGP) is routing protocol used between autonomous systems. This chapter concludes with a discussion of BGP routing and an implementation of BGP in a single-homed network.
Remote-Access Connections (3.1)
In this section, you learn how to select broadband remote-access technologies to support business requirements.
Broadband Connections (3.1.1)
In this topic, you compare remote-access broadband connection options for small- to medium-sized businesses.
What Is a Cable System? (3.1.1.1)
Accessing the Internet through a cable network is a popular option that teleworkers use to access their enterprise network. The cable system uses a coaxial cable that carries radio frequency (RF) signals across the network. Coaxial cable is the primary medium used to build cable TV systems.
Visit this website to learn more about the history of cable:
Modern cable systems offer customers advanced telecommunications services, including high-speed Internet access, digital cable television, and residential telephone service. Cable operators typically deploy hybrid fiber-coaxial (HFC) networks to enable high-speed transmission of data to cable modems located in a small office/home office (SOHO).
The Data over Cable Service Interface Specification (DOCSIS) is the international standard for adding high-bandwidth data to an existing cable system.
Figure 3-1 shows an example of a cable system.
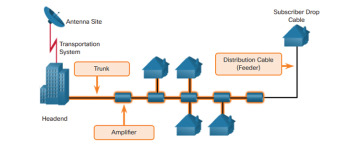
Figure 3-1 Cable System
The following describes the components shown in Figure 3-1:
Antenna site: The location of an antenna site is chosen for optimum reception of over-the-air, satellite, and sometimes point-to-point signals. The main receiving antennas and satellite dishes are located at the antenna site.
Transportation network: A transportation network links a remote antenna site to a headend or a remote headend to the distribution network. The transportation network can be microwave, coaxial, or fiber optic.
Headend: This is where signals are first received, processed, formatted, and then distributed downstream to the cable network. The headend facility is usually unmanned, under security fencing, and is similar to a telephone company central office (CO).
Amplifier: This is a device that regenerates an incoming signal to extend further through the network. Cable networks use various types of amplifiers in their transportation and distribution networks.
Subscriber drop: A subscriber drop connects the subscriber to the cable services. The subscriber drop is a connection between the feeder part of a distribution network and the subscriber terminal device (e.g., cable modem). The type of cable commonly used in a subscriber drop consists of radio grade (RG) series 6 (RG6) or series 59 (RG59) coaxial cable.
Cable Components (3.1.1.2)
Figure 3-2 shows an end-to-end cable topology.
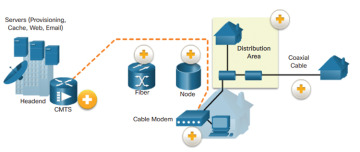
Figure 3-2 End-to-End Data Propagation over Cable
The following describes the components shown in Figure 3-2:
Cable modem termination system (CMTS): A CMTS is a component that exchanges digital signals with cable modem on a cable network. A headend CMTS communicates with CMs that are located in subscriber homes.
Fiber: The trunk portion of the cable network is usually fiber-optic cable.
Node: Nodes convert optical signals to RF signals.
Distribution area: A distribution network segment (feeder segment) is from 500 to as many as 2000 subscribers.
Coaxial cable: Coaxial feeder cables originate from the node and carry RF signals to the subscribers.
Cable modem: A cable modem enables you to receive data at high speeds. Typically, the cable modem attaches to a standard Ethernet card in the computer.
A headend CMTS communicates with CMs located in subscriber homes. The headend is actually a router with databases for providing Internet services to cable subscribers. The architecture is relatively simple, using an HFC network. The HFC network is a mixed optical-coaxial network in which optical fiber replaces the lower bandwidth coaxial cable. The fiber carries the same broadband content for Internet connections, telephone service, and streaming video as the coaxial cable carries.
In a modern HFC network, typically 500 to 2000 active data subscribers are connected to a cable network segment, all sharing the upstream and downstream bandwidth. DOCSIS standards are used to specify how data is exchanged between cable modem and the headend. For instance, the DOCSIS 3.1 standard supports downstream bandwidths (that is, from the headend to the subscriber) up to 10 Gb/s and upstream bandwidths (that is, from the subscriber to the headend) of 1 Gb/s.
What Is DSL? (3.1.1.3)
A digital subscriber line (DSL) is a means of providing high-speed connections over installed copper wires. DSL is one of the key teleworker solutions available.
Figure 3-3 shows a representation of bandwidth space allocation on a copper wire for asymmetric DSL (ADSL). The area labeled POTS (Plain Old Telephone System) identifies the frequency range used by the voice-grade telephone service. The area labeled ADSL represents the frequency space used by the upstream and downstream DSL signals. The area that encompasses both the POTS area and the ADSL area represents the entire frequency range supported by the copper wire pair.
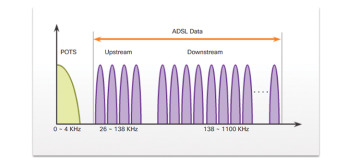
Figure 3-3 Asymmetric DSL in the Electromagnetic Spectrum
Another form of DSL technology is symmetric DSL (SDSL). All forms of DSL service are categorized as ADSL or SDSL, and there are several varieties of each type. ADSL provides higher downstream bandwidth to the user than upload bandwidth. SDSL provides the same capacity in both directions.
The different varieties of DSL provide different bandwidths, some with capabilities exceeding 40 Mb/s. The transfer rates are dependent on the actual length of the local loop, and the type and condition of the cabling. For satisfactory ADSL service, the loop must be less than 3.39 miles (5.46 km).
DSL Connections (3.1.1.4)
Service providers deploy DSL connections in the local loop. The connection is set up between a pair of modems on either end of a copper wire that extends between the customer premises equipment (CPE) and the DSL access multiplexer (DSLAM). A DSLAM is the device located at the CO of the provider; it concentrates connections from multiple DSL subscribers. A DSLAM is often built into an aggregation router.
Figure 3-4 shows the equipment needed to provide a DSL connection to a SOHO.
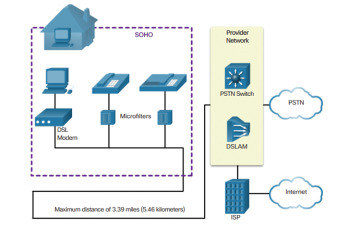
Figure 3-4 DSL Connections
The two important components in this topology are the DSL transceiver and the DSLAM:
DSL transceiver: Connects the computer of the teleworker to the DSL. Usually, the transceiver is a DSL modem connected to the computer using a USB or Ethernet cable. Typically, DSL transceivers are built into small routers with multiple switch ports suitable for home office use.
DSLAM: Located at the CO of the carrier, the DSLAM combines individual DSL connections from users into one high-capacity link to an ISP, and therefore, to the Internet.
A DSL micro filter (also known as a DSL filter) is required to connect devices such as phones or fax machines on the DSL network.
Figure 3-5 depicts modern DSL routers and broadband aggregation routers.
The advantage that DSL has over cable technology is that DSL is not a shared medium. Each user has a separate direct connection to the DSLAM. Adding users does not impede performance, unless the DSLAM Internet connection to the ISP, or the Internet, becomes saturated.

Figure 3-5 Example of DSL Routers
Wireless Connection (3.1.1.5)
Developments in broadband wireless technology are increasing wireless availability through three main technologies:
Municipal Wi-Fi
Cellular/mobile
Satellite Internet
The sections that follow describe these technologies in more detail.
Municipal Wi-Fi
Many municipal governments, often working with service providers, are deploying wireless networks. Some of these networks provide high-speed Internet access at no cost or for substantially less than the price of other broadband services. Other cities reserve their Wi-Fi networks for official use, providing police, firefighters, and city workers remote access to the Internet and municipal networks.
Most municipal wireless networks use a mesh of interconnected access points, as shown in Figure 3-6. Each access point is in range and can communicate with at least two other access points. The mesh blankets a particular area with radio signals.
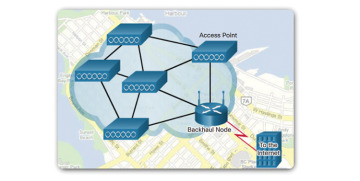
Figure 3-6 Municipal Wireless Network
Cellular/Mobile
Mobile phones use radio waves to communicate through nearby cell towers. The mobile phone has a small radio antenna. The provider has a much larger antenna that sits at the top of a tower, as shown in Figure 3-7.

Figure 3-7 Cellular Tower
Three common terms are used when discussing cellular/mobile networks:
Wireless Internet: A general term for Internet services from a mobile phone or from any device that uses the same technology.
2G/3G/4G wireless: Major changes to the mobile phone companies’ wireless networks through the evolution of the second, third, and fourth generations of wireless mobile technologies.
Long-Term Evolution (LTE): A newer and faster technology considered to be part of 4G technology.
Cellular/mobile broadband access consists of various standards such as 4G using LTE. A mobile phone subscription does not necessarily include a mobile broadband subscription. Cellular speeds continue to increase. For example, 4G LTE Category 10 supports up to 450 Mb/s download and 100 Mb/s upload.
Satellite Internet
Satellite Internet services are used in locations where land-based Internet access is not available or for temporary installations that are mobile. Internet access using satellites is available worldwide, including for providing Internet access to vessels at sea, airplanes in flight, and vehicles moving on land.
Figure 3-8 illustrates a two-way satellite system that provides Internet access to a home subscriber. Upload speeds are about one-tenth of the download speed. Download speeds range from 5 Mb/s to 25 Mb/s.
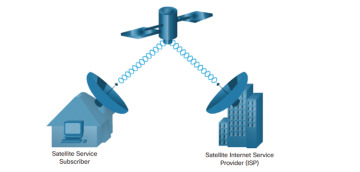
Figure 3-8 Two-Way Satellite Implementation
The primary installation requirement is for the antenna to have a clear view toward the equator, where most orbiting satellites are stationed. Trees and heavy rains can affect reception of the signals.
Select a Broadband Connection (3.1.2)
In this topic, you select an appropriate broadband connection for a given network requirement.
Comparing Broadband Solutions (3.1.2.1)
Each broadband solution has advantages and disadvantages. The ideal is to have a fiber-optic cable directly connected to the SOHO network. Some locations have only one option, such as cable or DSL. Some locations have only broadband wireless options for Internet connectivity.
If multiple broadband solutions are available, a cost-versus-benefit analysis should be performed to determine the best solution.
Some factors to consider in making a decision include
Cable: Bandwidth is shared by many users; upstream data rates are often slow during high-usage hours in areas with oversubscription.
DSL: Limited bandwidth is distance sensitive (in relation to the ISP’s central office); the upstream rate is proportionally quite small compared to the downstream rate.
Cellular/mobile: Coverage is often an issue, even within a SOHO where bandwidth is relatively limited.
Wi-Fi mesh: Most municipalities do not have a mesh network deployed; if it is available and the SOHO is in range, it is a viable option.
Satellite Internet: This option is expensive, has limited capacity per subscriber, but often provides access where no other access is possible.
PPPoE (3.2)
In this section, you configure a Cisco router with PPPoE.
PPPoE Overview (3.2.1)
In this topic, you learn how PPPoE operates.
PPPoE Motivation (3.2.1.1)
In addition to understanding the various technologies available for broadband Internet access, it is also important to understand the underlying data link layer protocol that the ISP uses to form a connection.
A data link layer protocol commonly used by ISPs is Point-to-Point Protocol (PPP). PPP can be used on all serial links, including those links created with dialup analog and ISDN modems. To this day, the link from a dialup user to an ISP, using analog modems, likely uses PPP.
Figure 3-9 shows a basic representation of that analog dial connection with PPP.
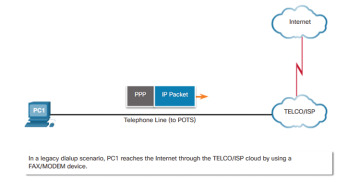
Figure 3-9 PPP Frames over Legacy Dialup Connection
Additionally, ISPs often use PPP as the data link protocol over broadband connections. There are several reasons for this. First, PPP supports the ability to assign IP addresses to remote ends of a PPP link. With PPP enabled, ISPs can use PPP to assign each customer one public IPv4 address. More importantly, PPP supports CHAP authentication. ISPs often want to use CHAP to authenticate customers because during authentication, ISPs can check accounting records to determine whether the customer’s bill is paid prior to letting the customer connect to the Internet.
These technologies came to market in the following order, with varying support for PPP:
1. Analog modems for dialup that could use PPP and CHAP
2. ISDN for dialup that could use PPP and CHAP
3. DSL, which did not create a point-to-point link and could not support PPP and CHAP
ISPs value PPP because of the authentication, accounting, and link-management features. Customers appreciate the ease and availability of the Ethernet connection; however, Ethernet links do not natively support PPP. PPP over Ethernet (PPPoE) provides a solution to this problem. As shown in Figure 3-10, PPPoE sends PPP frames encapsulated inside Ethernet frames.
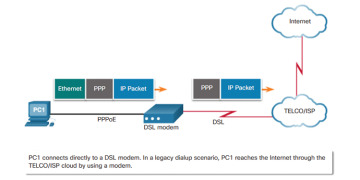
Figure 3-10 PPP Frames over an Ethernet Connection (PPPoE)
PPPoE Concepts (3.2.1.2)
As shown in Figure 3-11, the customer’s router is usually connected to a DSL modem using an Ethernet cable. PPPoE creates a PPP tunnel over an Ethernet connection. This allows PPP frames to be sent across the Ethernet cable to the ISP from the customer’s router. The modem converts the Ethernet frames to PPP frames by stripping the Ethernet headers. The modem then transmits these PPP frames on the ISP’s DSL network.

Figure 3-11 Tunneling to Create a PPP Link over Ethernet
Implement PPPoE (3.2.2)
In this topic, you implement a basic PPPoE connection on a client router.
PPPoE Configuration (3.2.2.1)
With the ability to send and receive PPP frames between the routers, the ISP could continue to use the same authentication model as with analog and ISDN. To make it all work, the client and ISP routers need additional configuration, including PPP configuration, as shown in Figure 3-12.
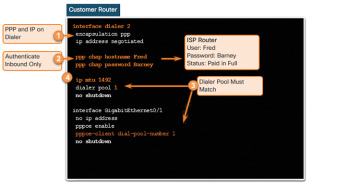
Figure 3-12 Steps for a PPPoE Customer Configuration
To understand the configuration, consider the following:
1. To create a PPP tunnel, the configuration uses a dialer interface. A dialer interface is a virtual interface. The PPP configuration is placed on the dialer interface, not the physical interface. The dialer interface is created using the interface dialer number global configuration command. The client can configure a static IP address but will more likely be automatically assigned a public IP address by the ISP.
2. The PPP CHAP configuration usually defines one-way authentication; therefore, the ISP authenticates the customer. The hostname and password configured on the customer router must match the hostname and password configured on the ISP router. Notice in Figure 3-12 that the CHAP username and password match the settings on the ISP router.
3. The physical Ethernet interface that connects to the DSL modem is then enabled with the pppoe enable interface configuration command. This command enables PPPoE and links the physical interface to the dialer interface. The dialer interface is linked to the Ethernet interface with the dialer pool number and pppoe-client dial-pool-number number interface configuration commands, using the same number. The dialer interface number does not have to match the dialer pool number.
4. The maximum transmission unit (MTU) should be lowered to 1492, versus the default of 1500, to accommodate the PPPoE headers.
PPPoE Verification (3.2.2.2)
As shown in Figure 3-13, the customer’s router is connected to the ISP router using DSL. Both routers have been configured for PPPoE.

Figure 3-13 Verifying the PPPoE Configuration
In Example 3-1, the show ip interface brief command is issued on R1 to verify the IPv4 address automatically assigned to the dialer interface by the ISP router.
Example 3-1 Verifying the Dialer Interface Is Up
R1# show ip interface brief Interface IP-Address OK? Method Status Protocol Embedded-Service-Engine0/0 unassigned YES unset administratively down down GigabitEthernet0/0 unassigned YES unset administratively down down GigabitEthernet0/1 unassigned YES unset up up Serial0/0/0 unassigned YES unset administratively down down Serial0/0/1 unassigned YES unset administratively down down Dialer2 10.1.3.1 YES IPCP up up Virtual-Access1 unassigned YES unset up up Virtual-Access2 unassigned YES unset up up R1#
As shown in Example 3-2, the show interface dialer command on R1 verifies the MTU and PPP encapsulation configured on the dialer interface.
Example 3-2 Verifying the MTU Size and Encapsulation
R1# show interface dialer 2
Dialer2 is up, line protocol is up (spoofing)
Hardware is Unknown
Internet address is 10.1.3.1/32
MTU 1492 bytes, BW 56 Kbit/sec, DLY 20000 usec,
reliability 255/255, txload 1/255, rxload 1/255
Encapsulation PPP, LCP Closed, loopback not set
Keepalive set (10 sec)
DTR is pulsed for 1 seconds on reset
<output omitted>
Example 3-3 displays the routing table on R1.
Example 3-3 Verifying the R1 Routing Table
R1# show ip route | begin Gateway
Gateway of last resort is 0.0.0.0 to network 0.0.0.0
S* 0.0.0.0/0 is directly connected, Dialer2
10.0.0.0/32 is subnetted, 2 subnets
C 10.1.3.1 is directly connected, Dialer2
C 10.1.3.2 is directly connected, Dialer2
R1#
Notice that two /32 host routes for 10.0.0.0 have been installed in R1’s routing table. The first host route is for the address assigned to the dialer interface. The second host route is the IPv4 address of the ISP. The installation of these two host routes is the default behavior for PPPoE.
As shown in Example 3-4, the show pppoe session command enables you to display information about currently active PPPoE sessions.
Example 3-4 Viewing the Current PPPoE Sessions
R1# show pppoe session
1 client session
Uniq ID PPPoE RemMAC Port VT VA State
SID LocMAC VA-st Type
N/A 1 30f7.0da3.1641 Gi0/1 Di2 Vi2 UP
30f7.0da3.0da1 UP
R1#
The output displays the local and remote Ethernet MAC addresses of both routers. The Ethernet MAC addresses can be verified by using the show interfaces command on each router.
PPPoE Troubleshooting (3.2.2.3)
After you ensure that the client router and DSL modem are connected with the proper cables, the cause of a PPPoE connection not functioning properly is usually one or more of the following reasons:
Failure in the PPP negotiation process
Failure in the PPP authentication process
Failure to adjust the TCP maximum segment size (MSS)
PPPoE Negotiation (3.2.2.4)
Verify PPP negotiation using the debug ppp negotiation command. Example 3-5 displays part of the debug output after R1’s G0/1 interface has been enabled.
Example 3-5 Examining the PPP Negotiation Process
R1# debug ppp negotiation *Sep 20 19:05:05.239: Vi2 PPP: Phase is AUTHENTICATING, by the peer *Sep 20 19:05:05.239: Vi2 LCP: State is Open <output omitted> *Sep 20 19:05:05.247: Vi2 CHAP: Using hostname from interface CHAP *Sep 20 19:05:05.247: Vi2 CHAP: Using password from interface CHAP *Sep 20 19:05:05.247: Vi2 CHAP: O RESPONSE id 1 len 26 from "Fred" *Sep 20 19:05:05.255: Vi2 CHAP: I SUCCESS id 1 len 4 <output omitted> *Sep 20 19:05:05.259: Vi2 IPCP: Address 10.1.3.2 (0x03060A010302) *Sep 20 19:05:05.259: Vi2 IPCP: Event[Receive ConfAck] State[ACKsent to Open] *Sep 20 19:05:05.271: Vi2 IPCP: State is Open *Sep 20 19:05:05.271: Di2 IPCP: Install negotiated IP interface address 10.1.3.2 *Sep 20 19:05:05.271: Di2 Added to neighbor route AVL tree: topoid 0, address 10.1.3.2 *Sep 20 19:05:05.271: Di2 IPCP: Install route to 10.1.3.2 R1# undebug all
The output is an example of what should be generated when PPP is correctly configured.
The four main points of failure in a PPP negotiation are as follows:
No response from the remote device (the ISP)
Link Control Protocol (LCP) not open
Authentication failure
IP Control Protocol (IPCP) failure
PPPoE Authentication (3.2.2.5)
After confirming with the ISP that it uses CHAP, verify that the CHAP username and password are correct. Example 3-6 shows the CHAP configuration on the dialer2 interface.
Example 3-6 Verify the CHAP Configuration
R1# show running-config | section interface Dialer2 interface Dialer2 mtu 1492 ip address negotiated encapsulation ppp dialer pool 1 ppp authentication chap callin ppp chap hostname Fred ppp chap password 0 Barney R1#
Re-examining the output of the debug ppp negotiation command in Example 3-7 verifies that the CHAP username is correct.
Example 3-7 Verify the CHAP Username
R1# debug ppp negotiation *Sep 20 19:05:05.239: Vi2 PPP: Phase is AUTHENTICATING, by the peer *Sep 20 19:05:05.239: Vi2 LCP: State is Open <output omitted> *Sep 20 19:05:05.247: Vi2 CHAP: Using hostname from interface CHAP *Sep 20 19:05:05.247: Vi2 CHAP: Using password from interface CHAP *Sep 20 19:05:05.247: Vi2 CHAP: O RESPONSE id 1 len 26 from "Fred" *Sep 20 19:05:05.255: Vi2 CHAP: I SUCCESS id 1 len 4 <output omitted> *Sep 20 19:05:05.259: Vi2 IPCP: Address 10.1.3.2 (0x03060A010302) *Sep 20 19:05:05.259: Vi2 IPCP: Event[Receive ConfAck] State[ACKsent to Open] *Sep 20 19:05:05.271: Vi2 IPCP: State is Open *Sep 20 19:05:05.271: Di2 IPCP: Install negotiated IP interface address 10.1.3.2 *Sep 20 19:05:05.271: Di2 Added to neighbor route AVL tree: topoid 0, address 10.1.3.2 *Sep 20 19:05:05.271: Di2 IPCP: Install route to 10.1.3.2 R1# undebug all
If the CHAP username or password were incorrect, the output from the debug ppp negotiation command would show an authentication failure message such as shown in Example 3-8.
Example 3-8 Authentication Failure Message
R1# *Sep 20 19:05:05.247: Vi2 CHAP: I FAILURE id 1 Len 26 MSG is "Authentication failure" R1#
PPPoE MTU Size (3.2.2.6)
Accessing some web pages might be a problem with PPPoE. When the client requests a web page, a TCP three-way handshake occurs between the client and the web server. During the negotiation, the client specifies the value of its TCP maximum segment size (MSS). The TCP MSS is the maximum size of the data portion in the TCP segment.
A host determines the value of its MSS field by subtracting the IP and TCP headers from the Ethernet maximum transmission unit (MTU). On an Ethernet interface, the default MTU is 1500 bytes. Subtracting the IPv4 header of 20 bytes and the TCP header of 20 bytes, the default MSS size will be 1460 bytes, as shown in Figure 3-14.
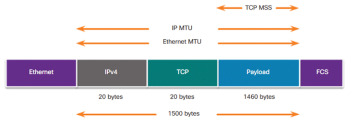
Figure 3-14 MTU and MSS
The default MSS size is 1460 bytes, when the default MTU is 1500 bytes; however, PPPoE supports an MTU of only 1492 bytes to accommodate the additional 8-byte PPPoE header, as shown in Figure 3-15.
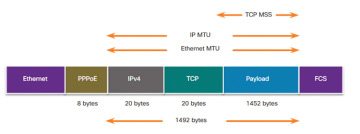
Figure 3-15 Adjusted MSS with PPPoE Header
You can verify the PPPoE MTU size in running configuration, as shown in Example 3-9. This disparity between the host and PPPoE MTU size can cause the router to drop 1500-byte packets and terminate TCP sessions over the PPPoE network.
Example 3-9 Verifying the MTU Size on the Dialer Interface
R1# show running-config | section interface Dialer2 interface Dialer2 mtu 1492 ip address negotiated encapsulation ppp <output omitted>
The ip tcp adjust-mss max-segment-size interface configuration command helps prevent TCP sessions from being dropped by adjusting the MSS value during the TCP three-way handshake. In most cases, the optimum value for the max-segment-size argument is 1452 bytes. Example 3-10 shows this configuration on R1’s LAN interface.
Example 3-10 Adjusting the TCP MSS
R1(config)# interface g0/0 R1(config-if)# ip tcp adjust-mss 1452
The TCP MSS value of 1452 plus the 20-byte IPv4 header, the 20-byte TCP header, and the 8-byte PPPoE header adds up to a 1500-byte MTU, as illustrated previously in Figure 3-15.
VPNs (3.3)
In this section, you learn how VPNs secure site-to-site and remote-access connectivity.
Fundamentals of VPNs (3.3.1)
In this topic, you learn about the benefits of VPN technology.
Introducing VPNs (3.3.1.1)
Organizations need secure, reliable, and cost-effective ways to interconnect multiple networks, such as allowing branch offices and suppliers to connect to a corporation’s headquarter network. Additionally, with the growing number of teleworkers, enterprises have an increasing need for secure, reliable, and cost-effective ways to connect employees working in small office/home office (SOHO) and other remote locations, with resources on corporate sites.
As shown in Figure 3-16, organizations use VPNs to create an end-to-end private network connection over third-party networks, such as the Internet. The tunnel eliminates the distance barrier and enables remote users to access central site network resources.
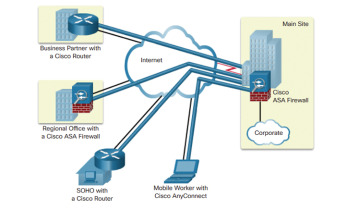
Figure 3-16 VPNs
A VPN is a private network created via tunneling over a public network, usually the Internet. A VPN is a communications environment in which access is strictly controlled to permit peer connections within a defined community of interest.
The first VPNs were strictly IP tunnels that did not include authentication or encryption of the data. For example, Generic Routing Encapsulation (GRE) is a tunneling protocol developed by Cisco that can encapsulate a wide variety of network layer protocol packet types inside IP tunnels. This creates a virtual point-to-point link to Cisco routers at remote points over an IP internetwork. However, GRE does not support encryption.
Today, a secure implementation of VPN with encryption, such as IPsec VPNs, is what is usually meant by virtual private networking.
To implement VPNs, a VPN gateway is necessary. The VPN gateway could be a router, a firewall, or a Cisco Adaptive Security Appliance (ASA). An ASA is a standalone firewall device that combines firewall, VPN concentrator, and intrusion prevention functionality into one software image.
Benefits of VPNs (3.3.1.2)
As shown in Figure 3-17, a VPN uses virtual connections that are routed through the Internet from the private network of an organization to the remote site or employee host. The information from a private network is securely transported over the public network to form a virtual network.
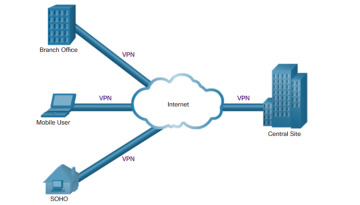
Figure 3-17 VPN Internet Connections
The benefits of a VPN include the following:
Cost savings: VPNs enable organizations to use cost-effective, third-party Internet transport to connect remote offices and remote users to the main site, thus eliminating expensive, dedicated WAN links and modem banks. Furthermore, with the advent of cost-effective, high-bandwidth technologies, such as DSL, organizations can use VPNs to reduce their connectivity costs while simultaneously increasing remote connection bandwidth.
Scalability: VPNs enable organizations to use the Internet infrastructure within ISPs and devices, which makes it easy to add new users. Therefore, organizations are able to add large amounts of capacity without adding significant infrastructure.
Compatibility with broadband technology: VPNs allow mobile workers and teleworkers to take advantage of high-speed, broadband connectivity, such as DSL and cable, to access to their organizations’ networks. Broadband connectivity provides flexibility and efficiency. High-speed, broadband connections also provide a cost-effective solution for connecting remote offices.
Security: VPNs can include security mechanisms that provide the highest level of security by using advanced encryption and authentication protocols that protect data from unauthorized access.
Types of VPNs (3.3.2)
In this topic, you learn about site-to-site and remote-access VPNs.
Site-to-Site VPNs (3.3.2.1)
A site-to-site VPN is created when devices on both sides of the VPN connection are aware of the VPN configuration in advance, as shown in Figure 3-18.

Figure 3-18 Site-to-Site VPNs
The VPN remains static, and internal hosts have no knowledge that a VPN exists. In a site-to-site VPN, end hosts send and receive normal TCP/IP traffic through a VPN “gateway.” The VPN gateway is responsible for encapsulating and encrypting outbound traffic for all traffic from a particular site. The VPN gateway then sends it through a VPN tunnel over the Internet to a peer VPN gateway at the target site. Upon receipt, the peer VPN gateway strips the headers, decrypts the content, and relays the packet toward the target host inside its private network.
A site-to-site VPN is an extension of a classic WAN network. Site-to-site VPNs connect entire networks to each other; for example, they can connect a branch office network to a company headquarters network. In the past, a leased-line or Frame Relay connection was required to connect sites, but because most corporations now have Internet access, these connections are commonly replaced with site-to-site VPNs.
Remote-Access VPNs (3.3.2.2)
Where a site-to-site VPN is used to connect entire networks, a remote-access VPN supports the needs of telecommuters, mobile users, and extranet, consumer-to-business traffic. A remote-access VPN is created when VPN information is not statically set up, but instead allows for dynamically changing information, and can be enabled and disabled. Remote-access VPNs support a client/server architecture, where the VPN client (remote host) gains secure access to the enterprise network via a VPN server device at the network edge, as shown Figure 3-19.
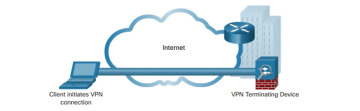
Figure 3-19 Remote-Access VPNs
Remote-access VPNs are used to connect individual hosts that must access their company network securely over the Internet. Internet connectivity used by telecommuters is typically a broadband connection.
VPN client software, such as the Cisco AnyConnect Secure Mobility Client software, is installed on the teleworker host. When the host sends traffic, the Cisco AnyConnect VPN Client software encapsulates, encrypts, and sends the traffic over the Internet to the destination VPN gateway. Upon receipt, the VPN gateway behaves as it does for site-to-site VPNs.
DMVPN (3.3.2.3)
Dynamic Multipoint VPN (DMVPN) is a Cisco software solution for building multiple VPNs in an easy, dynamic, and scalable manner. The goal is to simplify the configuration while easily and flexibly connecting central office sites with branch sites in a hub-and-spoke (or hub-to-spoke) topology, as shown in Figure 3-20.

Figure 3-20 DMVPN Hub-to-Spoke Tunnels
With DMVPNs, branch sites can also communicate directly with other branch sites, as shown in Figure 3-21.
DMVPN is built using the following technologies:
Next Hop Resolution Protocol (NHRP)
Multipoint Generic Routing Encapsulation (mGRE) tunnels
IP Security (IPsec) encryption
NHRP is a Layer 2 resolution and caching protocol similar to Address Resolution Protocol (ARP). NHRP creates a distributed mapping database of public IP addresses for all tunnel spokes. NHRP is a client/server protocol consisting of the NHRP hub known as the Next Hop Server (NHS) and the NHRP spokes known as the Next Hop Clients (NHCs). NHRP supports hub-and-spoke as well as spoke-to-spoke configurations.
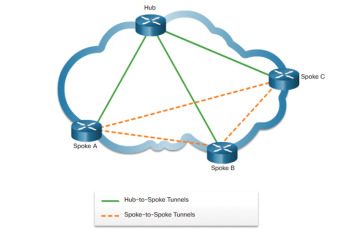
Figure 3-21 DMVPN Hub-to-Spoke and Spoke-to-Spoke Tunnels
Generic Routing Encapsulation (GRE) is a tunneling protocol developed by Cisco that can encapsulate a wide variety of protocol packet types inside IP tunnels. DMVPN makes use of Multipoint Generic Routing Encapsulation (mGRE) tunnel. An mGRE tunnel interface allows a single GRE interface to support multiple IPsec tunnels. With mGRE, dynamically allocated tunnels are created through a permanent tunnel source at the hub and dynamically allocated tunnel destinations, created as necessary, at the spokes. This reduces the size and simplifies the complexity of the configuration.
Like other VPN types, DMVPN relies on IPsec to provide secure transport of private information over public networks, such as the Internet.
GRE (3.4)
In this section, you implement a GRE tunnel.
GRE Overview (3.4.1)
In this topic, you learn about the purpose and benefits GRE tunnels.
GRE Introduction (3.4.1.1)
Generic Routing Encapsulation (GRE) is one example of a basic, nonsecure, site-to-site VPN tunneling protocol. GRE is a tunneling protocol developed by Cisco that can encapsulate a wide variety of protocol packet types inside IP tunnels. GRE creates a virtual point-to-point link to Cisco routers at remote points, over an IP internetwork.
GRE is designed to manage the transportation of multiprotocol and IP multicast traffic between two or more sites that may have only IP connectivity. It can encapsulate multiple protocol packet types inside an IP tunnel.
As shown in Figure 3-22, a tunnel interface supports a header for each of the following:
Passenger protocol: This is the original IPv4 or IPv6 packet that will be encapsulated by the carrier protocol. It could also be a legacy AppleTalk, DECnet, or IPX packet.
Carrier protocol: This is the encapsulation protocol such as GRE that encapsulates the passenger protocol.
Transport protocol: This is the delivery protocol such as IP that carries the carrier protocol.
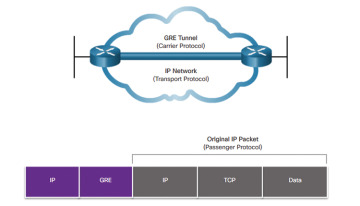
Figure 3-22 Generic Routing Encapsulation
GRE Characteristics (3.4.1.2)
GRE is a tunneling protocol developed by Cisco that can encapsulate a wide variety of protocol packet types inside IP tunnels, creating a virtual point-to-point link to Cisco routers at remote points over an IP internetwork. IP tunneling using GRE enables network expansion across a single-protocol backbone environment. It does this by connecting multiprotocol subnetworks in a single-protocol backbone environment.
GRE has these characteristics:
GRE is defined as an IETF standard (RFC 2784).
GRE is identified as IP protocol 47 in the Transport protocol IP protocol field.
GRE encapsulation includes a protocol type field in its header to provide multiprotocol support. Protocol types are defined in RFC 1700 as “EtherTypes.”
GRE is stateless, which means that, by default, it does not include any flow-control mechanisms.
GRE does not include any strong security mechanisms to protect its payload.
The GRE header consumes at least 24 bytes of additional overhead for tunneled packets.
Figure 3-23 illustrates the GRE header components.
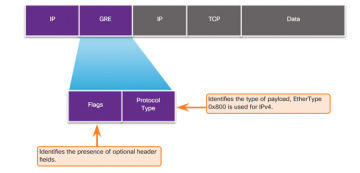
Figure 3-23 Header for GRE Encapsulated Packet Header

Activity 3.4.1.3: Identify GRE Characteristics
Implement GRE (3.4.2)
In this topic, you learn how to troubleshoot a site-to-site GRE tunnel.
Configure GRE (3.4.2.1)
The topology displayed in Figure 3-24 will be used to create a GRE VPN tunnel between two sites.
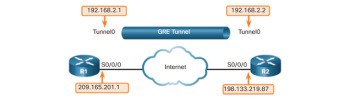
Figure 3-24 GRE Tunnel Configuration Topology
To implement a GRE tunnel, the network administrator must know the reachable IP addresses of the endpoints.
There are five steps to configuring a GRE tunnel:
Step 1. Create a tunnel interface using the interface tunnel number global configuration command.
Step 2. Configure an IP address for the tunnel interface using the ip address ip-address interface configuration command. This is normally a private IP address.
Step 3. Specify the tunnel source IP address or source interface using the tunnel source {ip-address | interface-name} interface configuration command.
Step 4. Specify the tunnel destination IP address using the tunnel destination ip-address interface configuration command.
Step 5. (Optional) Specify GRE tunnel mode as the tunnel interface mode using the tunnel mode gre protocol interface configuration command. GRE tunnel mode is the default tunnel interface mode for Cisco IOS software.
The sample configuration in Example 3-11 illustrates a basic GRE tunnel configuration for R1 and R2.
Example 3-11 R1 and R2 GRE Tunnel Configuration
R1(config)# interface Tunnel0 R1(config-if)# ip address 192.168.2.1 255.255.255.0 R1(config-if)# tunnel source 209.165.201.1 R1(config-if)# tunnel destination 209.165.201.2 R1(config-if)# tunnel mode gre ip R1(config-if)# exit R1(config)# router ospf 1 R1(config-router)# network 192.168.2.0 0.0.0.255 area 0 R2(config)# interface Tunnel0 R2(config-if)# ip address 192.168.2.2 255.255.255.0 R2(config-if)# tunnel source 209.165.201.2 R2(config-if)# tunnel destination 209.165.201.1 R2(config-if)# tunnel mode gre ip R2(config-if)# exit R2(config)# router ospf 1 R2(config-router)# network 192.168.2.0 0.0.0.255 area 0
The minimum configuration requires specification of the tunnel source and destination addresses. The IP subnet must also be configured to provide IP connectivity across the tunnel link. Both tunnel interfaces have the tunnel source set using the IP address of their local serial S0/0/0 interface and the tunnel destination set to the IP address of the peer router serial S0/0/0 interface. The tunnel interface IP address is typically assigned a private IP address. Finally, OSPF is configured to advertise the tunnel network route over the GRE tunnel.
Table 3-1 provides the individual GRE tunnel command descriptions.
Table 3-1 GRE Configuration Command Syntax
| Command | Description |
|---|---|
| ip address ip_address mask | Specifies the IP address of the tunnel interface |
| tunnel source ip_address | Specifies the tunnel source IP address, in interface tunnel configuration mode |
| tunnel destination ip_address | Specifies the tunnel destination IP address, in interface tunnel configuration mode |
| tunnel mode gre ip | Specifies GRE tunnel mode as the tunnel interface mode, in interface tunnel configuration mode |
Verify GRE (3.4.2.2)
Several commands can be used to monitor and troubleshoot GRE tunnels. To determine whether the tunnel interface is up or down, use the show ip interface brief and show interface tunnel number privileged EXEC commands, as demonstrated in Example 3-12.
Example 3-12 Verifying GRE
R1# show ip interface brief | include Tunnel
Tunnel0 192.168.2.1 YES manual up up
R1#
R1# show interface Tunnel 0
Tunnel0 is up, line protocol is up
Hardware is Tunnel
Internet address is 192.168.2.1/24
MTU 17916 bytes, BW 100 Kbit/sec, DLY 50000 usec,
reliability 255/255, txload 1/255, rxload 1/255
Encapsulation TUNNEL, loopback not set
Keepalive not set
Tunnel source 209.165.201.1, destination 209.165.201.2
Tunnel protocol/transport GRE/IP
<output omitted>
The first command verifies that the tunnel 0 interface is up and has an IP address assigned to it. The second command verifies the state of a GRE tunnel, the tunnel source and destination addresses, and the GRE mode supported. The line protocol on a GRE tunnel interface is up as long as there is a route to the tunnel destination. Before a GRE tunnel is implemented, IP connectivity must already be in effect between the IP addresses of the physical interfaces on opposite ends of the potential GRE tunnel.
A routing protocol could also be configured to exchange route information over the tunnel interface. For example if OSPF had also been configured to exchange routes over the GRE tunnel, you could verify that an OSPF adjacency had been established using the show ip ospf neighbor command.
In Example 3-13, note that the peering address for the OSPF neighbor is on the IP network created for the GRE tunnel.
Example 3-13 Verifying OSPF Adjacency via GRE Tunnel
R1# show ip ospf neighbor Neighbor ID Pri State Dead Time Address Interface 209.165.201.2 0 FULL/ - 00:00:37 192.168.2.2 Tunnel0
GRE is considered a VPN because it is a private network that is created by tunneling over a public network. Using encapsulation, a GRE tunnel creates a virtual point-to-point link to Cisco routers at remote points over an IP internetwork.
The advantages of GRE are that it can be used to tunnel non-IP traffic over an IP network, allowing for network expansion by connecting multiprotocol subnetworks across a single-protocol backbone environment. GRE also supports IP multicast tunneling. This means that routing protocols can be used across the tunnel, enabling dynamic exchange of routing information in the virtual network. Finally, it is common practice to create IPv6 over IPv4 GRE tunnels, where IPv6 is the encapsulated protocol and IPv4 is the transport protocol. In the future, these roles will likely be reversed as IPv6 takes over as the standard IP protocol.
However, GRE does not provide encryption or any other security mechanisms. Therefore, data sent across a GRE tunnel is not secure. If secure data communication is needed, IPsec or Secure Sockets Layer (SSL) VPNs should be configured.
Troubleshoot GRE (3.4.2.3)
Issues with GRE are usually due to one or more of the following misconfigurations:
The tunnel interface IP addresses are not on the same network or the subnet masks do not match.
The interfaces for the tunnel source and/or tunnel destination are not configured with the correct IP address or are in the down state.
Static or dynamic routing is not properly configured.
Figure 3-25 shows the GRE configuration topology.
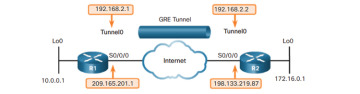
Figure 3-25 GRE Tunnel Configuration Topology
Use the show ip interface brief command on both routers to verify that the tunnel interface is up and configured with the correct IP addresses for the physical interface and the tunnel interface. Also, verify that the source interface on each router is up and configured with the correct IP addresses, as shown in Example 3-14.
Example 3-14 Verifying That All Necessary Interfaces Are Up
R1# show ip interface brief <some output omitted> Interface IP-Address OK? Method Status Protocol Serial0/0/0 209.165.201.1 YES manual up up Loopback0 10.0.0.1 YES manual up up Tunnel0 192.168.2.1 YES manual up up R1# R2# show ip interface brief <some output omitted> Interface IP-Address OK? Method Status Protocol Serial0/0/0 198.133.219.87 YES manual up up Loopback0 172.16.0.1 YES manual up up Tunnel0 192.168.2.2 YES manual up up R2#
Routing can cause an issue. Both routers need a default route pointing to the Internet. Also, both routers need the correct dynamic or static routing configured. You can use the show ip ospf neighbor command to verify neighbor adjacency. Regardless of the routing used, you can also use show ip route to verify that networks are being passed between the two routers, as shown in Example 3-15.
Example 3-15 Verify That Networks Are Being Routed
R1# show ip route ospf
172.16.0.0/32 is subnetted, 1 subnets
O 172.16.0.0 [110/1001] via 192.168.2.2, 00:19:44, Tunnel0
R1#
R2# show ip route ospf
10.0.0.0/32 is subnetted, 1 subnets
O 10.0.0.1 [110/1001] via 192.168.2.1, 00:20:35, Tunnel0
R2#
eBGP (3.5)
In this section, you implement eBGP in a single-homed remote-access network.
BGP Overview (3.5.1)
In this topic, you learn about the basic BGP features.
IGP and EGP Routing Protocols (3.5.1.1)
RIP, EIGRP, and OSPF are Interior Gateway Protocols (IGPs). ISPs and their customers, such as corporations and other enterprises, usually use an IGP to route traffic within their networks. IGPs are used to exchange routing information within a company network or an autonomous system (AS).
Border Gateway Protocol (BGP) is an Exterior Gateway Protocol (EGP) used for the exchange of routing information between autonomous systems, such as ISPs, companies, and content providers (such as YouTube and Netflix).
In BGP, every AS is assigned a unique 16-bit or 32-bit AS number (ASN), which uniquely identifies it on the Internet. Figure 3-26 shows an example of how IGPs are interconnected using BGP.
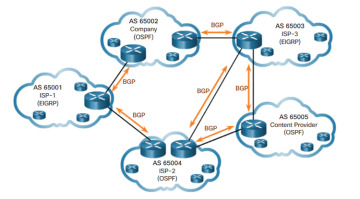
Figure 3-26 IGP and EGP Routing Protocols
Internal routing protocols use a specific metric, such as OSPF’s cost, for determining the best paths to destination networks. BGP does not use a single metric like IGPs. BGP routers exchange several path attributes including a list of AS numbers (hop by hop) necessary to reach a destination network.
For example, in Figure 3-26, AS 65002 may use the AS-path of 65003 and 65005 to reach a network within the content provider AS 65005. BGP is known as a path vector routing protocol.
BGP updates are encapsulated over TCP on port 179. Therefore, BGP inherits the connection-oriented properties of TCP, which ensures that BGP updates are transmitted reliably.
IGP routing protocols are used to route traffic within the same organization and administered by a single organization. In contrast, BGP is used to route between networks administered by two different organizations. An AS uses BGP to advertise its networks and, in some cases, networks that it learned about from other autonomous systems, to the rest of the Internet.
eBGP and iBGP (3.5.1.2)
Two routers exchanging BGP routing information are known as BGP peers. As shown in Figure 3-27, there are two types of BGP, as described in the list that follows.
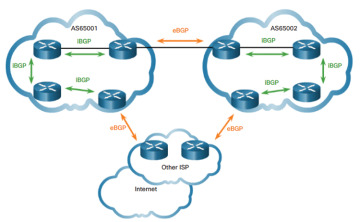
Figure 3-27 eBGP and iBGP Comparison
External BGP (eBGP): External BGP is a BGP configuration between two routers in different autonomous systems. For example, eBGP would be used to connect an enterprise AS to a service provider AS.
Internal BGP (iBGP): Internal BGP is a BGP configuration between two routers in the same autonomous systems. For example, iBGP would be used between routers in a service provider AS.
This course focuses on eBGP only.
BGP Design Considerations (3.5.2)
In this topic, you learn about BGP design considerations.
When to Use BGP (3.5.2.1)
The use of BGP is most appropriate when an AS has connections to multiple autonomous systems. This is known as multihomed. Each AS in Figure 3-28 is multihomed because each AS has connections to at least two other autonomous systems or BGP peers.
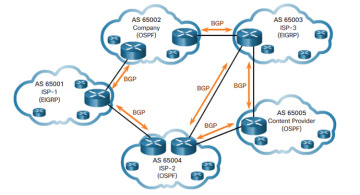
Figure 3-28 Multihomed
When Not to Use BGP (3.5.2.2)
BGP should not be used when at least one of the following conditions exist:
There is a single connection to the Internet or another AS. This is known as single-homed. In this case, Company-A may run an IGP with the ISP, or Company-A and the ISP each use static routes, as shown in Figure 3-29. Although it is recommended only in unusual situations, for the purposes of this course, you will configure single-homed BGP.
There is a limited understanding of BGP. A misconfiguration of a BGP router can have far-reaching effects beyond the local AS, negatively impacting routers throughout the Internet.

Figure 3-29 Single-Homed
BGP Options (3.5.2.3)
BGP is used by autonomous systems to advertise networks that originated within their AS or, in the case of ISPs, the networks that originated from other autonomous systems.
For example, a company connecting to its ISP using BGP would advertise its network addresses to the ISP. The ISP would then advertise these networks to other ISPs (BGP peers). Eventually, all other autonomous systems on the Internet would learn about the networks initially originated by the company.
An organization can choose to implement BGP in a multihomed environment in three common ways.
Default Route Only
ISPs advertise a default route to Company-A, as shown in Figure 3-30.
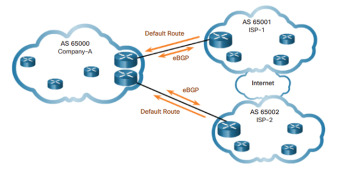
Figure 3-30 Default Route Only
The arrows indicate that the default is configured on the ISPs, not on Company-A. This is the simplest method to implement BGP; however, because the company receives only a default route from both ISPs, suboptimal routing may occur. For example, Company-A may choose to use ISP-1’s default route when sending packets to a destination network in ISP-2’s AS.
Default Route and ISP Routes
ISPs advertise their default route and their network to Company-A, as shown in Figure 3-31.
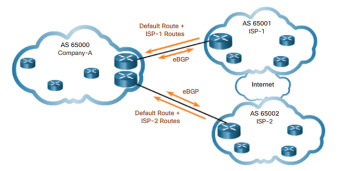
Figure 3-31 Default Route and ISP Routes
This option allows Company-A to forward traffic to the appropriate ISP for networks advertised by that ISP. For example, Company-A would choose ISP-1 for networks advertised by ISP-1. For all other networks, one of the two default routes can be used, which means suboptimal routing may still occur for all other Internet routes.
All Internet Routes
ISPs advertise all Internet routes to Company-A, as shown in Figure 3-32.
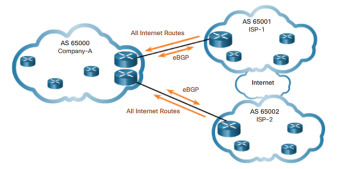
Figure 3-32 All Internet Routes
Because Company-A receives all Internet routes from both ISPs, Company-A can determine which ISP to use as the best path to forward traffic for any network. Although this approach solves the issue of suboptimal routing, the BGP router would require sufficient resources to maintain well over 500,000 Internet networks.
eBGP Branch Configuration (3.5.3)
In this topic, you configure an eBGP branch connection.
Steps to Configure eBGP (3.5.3.1)
To implement eBGP for this course, you need to complete the following tasks:
Step 1. Enable BGP routing.
Step 2. Configure BGP neighbor(s) (peering).
Step 3. Advertise network(s) originating from this AS.
Table 3-2 lists the command syntax and a description for basic eBGP configuration.
Table 3-2 BGP Configuration Commands
| Command | Description |
|---|---|
| Router(config)# router bgp as-number | Enables a BGP routing process and places the router in router configuration mode. |
| Router(config-router)# neighbor ip-address remote-as as-number | Specifies a BGP neighbor. The as-number is the neighbor’s AS number. |
| Router(config-router)# network network-address [mask network-mask] | Advertises a network address to an eBGP neighbor as being originated by this AS. The network-mask is the subnet mask of the network. |
BGP Sample Configuration (3.5.3.2)
In this single-homed BGP topology, Company-A in AS 65000 uses eBGP to advertise its 198.133.219.0/24 network to ISP-1 at AS 65001. ISP-1 advertises a default route in its eBGP updates to Company-A.
Figure 3-33 shows the BGP configuration topology.

Figure 3-33 BGP Configuration Topology
Example 3-16 shows the BGP configuration for Company-A and ISP-1. Customers typically use private IPv4 address space for internal devices within their own network. Using Network Address Translation (NAT), the Company-A router translates these private IPv4 addresses to one of its public IPv4 addresses, advertised by BGP to the ISP.
Example 3-16 Company-A and ISP BGP Configuration
Company-A(config)# router bgp 65000 Company-A(config-router)# neighbor 209.165.201.1 remote-as 65001 Company-A(config-router)# network 198.133.219.0 mask 255.255.255.0 ISP-1(config)# router bgp 65001 ISP-1(config-router)# neighbor 209.165.201.2 remote-as 65000 ISP-1(config-router)# network 0.0.0.0
The router bgp global configuration command enables BGP and identifies the AS number for Company-A. A router can belong to only a single AS, so only a single BGP process can run on a router.
The neighbor router configuration command identifies the BGP peer IP address and AS number. Notice that the ISP AS number is different than the Company-A AS number. This informs the BGP process that the neighbor is in a different AS and is therefore an external BGP neighbor.
The network network-address [mask network-mask] router configuration command enters the network-address into the local BGP table. The BGP table contains all routes learned via BGP or advertised using BGP. eBGP will then advertise the network-address to its eBGP neighbors.
The mask network-mask command parameter must be used when the network advertised is different from its classful equivalent. In this example, the 198.133.219.0/24 is equivalent to a class C network. Class C networks have a /24 subnet mask, so in this case the mask option is not required. If Customer-A were advertising the 198.133.0.0/16 network, the mask option would be required. Otherwise, BGP would advertise the network with a /24 classful mask.
The eBGP commands on the ISP-1 router are similar to the configuration on Company-A. Notice how the network 0.0.0.0 router configuration command is used to advertise a default network to Company-A.
Verify eBGP (3.5.3.3)
You can use three commands to verify eBGP, as described in Table 3-3.
Table 3-3 BGP Verification Commands
| Command | Description |
|---|---|
| Router# show ip route | Verify routes advertised by the BGP neighbor are present in the IPv4 routing table |
| Router# show ip bgp | Verify that received and advertised IPv4 networks are in the BGP table |
| Router# show ip bgp summary | Verify IPv4 BGP neighbors and other BGP information |
Example 3-17 shows the output for Company-A’s IPv4 routing table. Notice how the origin code B identifies that the route was learned using BGP. Specifically, in this example, Company-A has received a BGP advertised default route from ISP-1.
Example 3-17 Verifying BGP Routes Are in the Table
Company-A# show ip route | include Gateway
Gateway of last resort is 209.165.201.1 to network 0.0.0.0
B* 0.0.0.0/0 [20/0] via 209.165.201.1, 00:36:03
10.0.0.0/8 is variably subnetted, 2 subnets, 2 masks
C 198.133.219.0/24 is directly connected, GigabitEthernet0/0
L 198.133.219.1/32 is directly connected, GigabitEthernet0/0
209.165.201.0/24 is variably subnetted, 2 subnets, 2 masks
C 209.165.201.0/27 is directly connected, GigabitEthernet0/1
L 209.165.201.2/32 is directly connected, GigabitEthernet0/1
Company-A#
Example 3-18 shows the output of Company-A’s BGP table.
Example 3-18 Verifying BGP
Company-A# show ip bgp
BGP table version is 3, local router ID is 209.165.201.2
Status codes: s suppressed, d damped, h history, * valid, > best, i - internal,
r RIB-failure, S Stale, m multipath, b backup-path, f RT-Filter,
x best-external, a additional-path, c RIB-compressed,
Origin codes: i - IGP, e - EGP, ? - incomplete
RPKI validation codes: V valid, I invalid, N Not found
Network Next Hop Metric LocPrf Weight Path
*> 0.0.0.0 209.165.201.1 0 0 65001 i
*> 198.133.219.0/24 0.0.0.0 0 32768 i
Company-A#
The first entry 0.0.0.0 with a next hop of 209.165.201.1 is the default route advertised by ISP-1. The AS path displays the single AS of 65001 because the 0.0.0.0/0 network advertised by ISP-1 originated from the same AS. Most BGP table entries show multiple autonomous system numbers in the path, listing the sequence of AS numbers required to reach the destination network.
The second entry 198.133.219.0/24 is the network advertised by the Company-A router to ISP-1. The next hop address of 0.0.0.0 indicates that the 198.133.219.0/24 network originated from this router.
Example 3-19 displays the status of BGP connection on Company-A. The first line displays the local IPv4 address used to peer with another BGP neighbor and this router’s local AS number. The address and AS number of the remote BGP neighbor are shown at the bottom of the output.
Example 3-19 Verify BGP Summary
Company-A# show ip bgp summary BGP router identifier 209.165.201.2, local AS number 65000 BGP table version is 3, main routing table version 3 2 network entries using 288 bytes of memory 2 path entries using 160 bytes of memory 2/2 BGP path/bestpath attribute entries using 320 bytes of memory 1 BGP AS-PATH entries using 24 bytes of memory 0 BGP route-map cache entries using 0 bytes of memory 0 BGP filter-list cache entries using 0 bytes of memory BGP using 792 total bytes of memory BGP activity 2/0 prefixes, 2/0 paths, scan interval 60 secs Neighbor V AS MsgRcvd MsgSent TblVer InQ OutQ Up/Down State/PfxRcd 209.165.201.1 4 65001 66 66 3 0 0 00:56:11 1 Company-A#
Check Your Understanding Questions
Complete all the review questions listed here to test your understanding of the topics and concepts in this chapter. The appendix “Answers to the ‘Check Your Understanding’ Questions” lists the answers.
PPPoE
QoS
VPN
WiMax
Authentication server
Broadband Internet connection
VPN client software or VPN-enabled router
Multifunction security appliance
VPN server or concentrator
DSL has no distance limitations.
DSL is faster.
DSL is not a shared medium.
DSL upload and download speeds are always the same.
Copper
Fiber
Radio frequency
Wireless
DSL
ISDN
PPPoE
QoS
To accommodate the PPPoE headers
To enable CHAP authentication
To establish a secure tunnel with less overhead?
To reduce congestion on the DSL link
An MTU size of 1492 bytes is configured on the Ethernet interface.
The customer router CHAP username and password are independent of what is configured on the ISP router.
The dialer pool command is applied to the Ethernet interface to link it to the dialer interface.
The Ethernet interface does not have an IP address.
The PPP configuration is on the dialer interface.
dialer pool 2
interface dialer 2
interface gigabitethernet 0/2
ppp chap hostname 2
ppp chap password 2
pppoe-client dial-pool-number 2
A dedicated ISP
A GRE IP tunnel
A leased line
A VPN gateway
Individual hosts can enable and disable the VPN connection.
Internal hosts send normal, unencapsulated packets.
The VPN connection is not statically defined.
VPN client software is installed on each host.
A branch office that connects securely to a central site
A central site that connects to a SOHO site without encryption
A mobile user who connects to a router at a central site
A mobile user who connects to a SOHO site
It provides interdomain routing between autonomous systems.
It is an advanced distance vector routing protocol.
It uses cost as its metric.
It is a link-state routing protocol.
It uses bandwidth and delay as its metric.
It is a policy-based routing protocol.
All BGP routers in the same domain share routing information by default
BGP routers that are configured with the same network command
BGP routers that are configured with the same peer command
BGP routers that are identified with the neighbor command
BGP is an IGP used to exchange routing information with another AS.
BGP updates are encapsulated using TCP port 179.
Every AS is assigned a unique 160-bit AS number (ASN).
Use BGP when there is a single connection to the Internet or another AS.
R1(config-router)# neighbor 209.165.201.1 remote-as 5000
R1(config-router)# neighbor 209.165.201.1 remote-as 10000
R1(config-router)# peer 209.165.201.1 remote-as 5000
R1(config-router)# peer 209.165.201.1 remote-as 10000
1. Which technology provides a secure connection between a SOHO and the headquarters office?
2. Which two network components does a teleworker require to connect remotely and securely from home to the corporate network? (Choose two.)
3. What advantage does DSL have compared to cable technology?
4. Which medium is used for delivering data via DSL technology through PSTN?
5. What technology provides service providers the capability to use authentication, accounting, and link management features to customers over Ethernet networks?
6. Why is the MTU for a PPPoE DSL configuration reduced from 1500 bytes to 1492?
7. What are two characteristics of a PPPoE configuration on a Cisco customer router? (Choose two.)
8. When PPPoE is configured on a customer router, which two commands must have the same value for the configuration to work? (Choose two.)
9. A network design engineer is planning the implementation of a cost-effective method to interconnect multiple networks securely over the Internet. Which type of technology is required?
10. Which statement describes a feature of site-to-site VPNs?
11. Which remote-access implementation scenario will support the use of Generic Routing Encapsulation tunneling?
12. Which two statements are key characteristics of BGP? (Choose two.)
13. Which BGP routers will become peers and share routing information?
14. Which of the following BGP statements is true?
15. Assume R1 is in AS 5000 and wants to establish an eBGP peer relationship with another router. Which of the following commands would correctly configure an eBGP relationship?
