This sample chapter from IT Essentials Companion Guide v6, 6th Edition, covers basic safety practices for the workplace, hardware and software tools, and the disposal of hazardous materials. Safety guidelines help protect individuals from accidents and injury. They also help to protect equipment from damage. Some of these guidelines are designed to protect the environment from contamination caused by improperly discarded materials.
Objectives
Upon completion of this chapter, you will be able to answer the following questions:
What are safe working conditions and procedures?
What procedures help protect equipment and data?
What procedures help to properly dispose of hazardous computer components and related material? What tools and software are used with personal computer components and what is their purpose?
What is proper tool use?
Key Terms
This chapter uses the following key terms. You can find the definitions in the Glossary.
Electrostatic discharge (ESD) Page 76
Electromagnetic interference (EMI) Page 77
Brownout Page 78
Spike Page 78
Noise Page 78
Blackout Page 78
Power surge Page 78
Surge suppressor Page 78
Standby power supply (SPS) Page 78
Uninterruptible power supply (UPS) Page 78
material safety and data sheet (MSDS) Page 80
tone generator and probe Page 86
History of repairs Page 90
antistatic wrist strap Page 83
antistatic mat Page 83
Power supply tester Page 94
Cable tester Page 94
Loopback plug Page 94
Multimeter Page 94
Disk Management Page 88
Format Page 88
CHKDSK Page 88
System File Checker (SFC) Page 88
Windows Action Center Page 89
Window Firewall Page 89
Introduction (2.0)
Safety is an important topic and exercise in the workplace. Safety guidelines help protect individuals from accidents and injury. They also help to protect equipment from damage.
Welcome (2.0.1)
The consequences of poor safety practices in the workplace can result in serious injury, increased equipment damage, harm to the environment, and other problems. Even a small incident will decrease productivity and increase costs. It is essential for all employees to understand safety at work.
Introduction to Lab Procedures and Tool Use (2.0.1.1)
This chapter covers basic safety practices for the workplace, hardware and software tools, and the disposal of hazardous materials. Safety guidelines help protect individuals from accidents and injury. They also help to protect equipment from damage. Some of these guidelines are designed to protect the environment from contamination caused by improperly discarded materials.
Safe Lab Procedures (2.1)
Everyone must understand and follow safety procedures.
Procedures to Protect People (2.1.1)
Safe working conditions help prevent injury to people and damage to computer equipment. A safe workspace is clean, organized, and properly lit.
General Safety (2.1.1.1)
Follow safety guidelines to prevent cuts, burns, electrical shock, and damage to eyesight. As a best practice, make sure that a fire extinguisher and first-aid kit are available. Poorly placed or unsecured cables can cause tripping hazards in a network installation. Cable management techniques such as installation of cables in conduit or cable trays help to prevent hazards.
This is a partial list of basic safety precautions to use when working on a computer:
Remove your watch and jewelry and secure loose clothing.
Turn off the power and unplug equipment before performing service.
Cover sharp edges inside the computer case with tape.
Never open a power supply or a monitor with a built-in power supply.
Do not touch areas in printers that are hot or that use high voltage.
Know where the fire extinguisher is located and how to use it.
Keep food and drinks out of your workspace.
Keep your workspace clean and free of clutter.
Bend your knees when lifting heavy objects to avoid injuring your back.
Wear safety goggles to prevent damage to eyesight.
Before cleaning or repairing equipment, make sure that your tools are in good condition. Clean, repair, or replace items that are not functioning adequately.
Electrical Safety (2.1.1.2)
Follow electrical safety guidelines to prevent electrical fires, injuries, and fatalities.
Some printer parts become hot during use, and other parts, such as power supplies, contain high voltage. Check the printer manual for the location of high-voltage components. Some components retain a high voltage even after the printer is turned off. Make sure that the printer has had time to cool before making the repair.
Electrical devices have certain power requirements. For example, AC adapters are manufactured for specific laptops. Exchanging AC adapters with a different type of laptop or device may cause damage to both the AC adapter and the laptop.
Fire Safety (2.1.1.3)
Follow fire safety guidelines to protect lives, structures, and equipment. To avoid an electrical shock and to prevent damage to the computer, turn off and unplug the computer before beginning a repair.
Fire can spread rapidly and be very costly. Proper use of a fire extinguisher can prevent a small fire from getting out of control. Use the memory aid P-A-S-S to remember the basic rules of fire extinguisher operation:
P: Pull the pin.
A: Aim at the base of the fire, not at the flames.
S: Squeeze the lever.
S: Sweep the nozzle from side to side.
Be familiar with the types of fire extinguishers used in your country or region. Each type of fire extinguisher has specific chemicals to fight different types of fires:
Paper, wood, plastics, cardboard
Gasoline, kerosene, organic solvents
Electrical equipment
Combustible metals
When working with computer components, be alert for odors emitting from computers and electronic devices. When electronic components overheat or short out, they emit a burning smell. If there is a fire, follow these safety procedures:
Never fight a fire that is out of control or not contained.
Always have a planned fire escape route before beginning any work.
Get out of the building quickly.
Contact emergency services for help.
Locate and read the instructions on the fire extinguishers in your workplace before you have to use them.
Procedures to Protect Equipment and Data (2.1.2)
Replacing equipment and recovering data is expensive and time consuming. This section identifies potential threats to systems and descries procedures to help prevent loss and damage.
ESD and EMI (2.1.2.1)
Replacing equipment and recovering data is expensive and time consuming. This section identifies potential threats to systems and describes procedures to help prevent loss and damage.
Electrostatic Discharge
Electrostatic discharge (ESD) can occur when there is a buildup of an electric charge (static electricity) that exists on a surface which comes into contact with another, differently charged surface. ESD can cause damage to computer equipment if not discharged properly. Follow proper handling guidelines, be aware of environmental issues, and use equipment that stabilizes power to prevent equipment damage and data loss.
At least 3,000 volts of static electricity must build up before a person can feel ESD. For example, static electricity can build up on you as you walk across a carpeted floor. When you touch another person, you both receive a shock. If the discharge causes pain or makes a noise, the charge was probably above 10,000 volts. By comparison, less than 30 volts of static electricity can damage a computer component.
ESD can cause permanent damage to electrical components. Follow these recommendations to help prevent ESD damage:
Keep all components in antistatic bags until you are ready to install them.
Use grounded mats on workbenches.
Use grounded floor mats in work areas.
Use antistatic wrist straps when working on computers.
Electromagnetic Interference
Electromagnetic interference (EMI) is the intrusion of outside electromagnetic signals in a transmission media, such as copper cabling. In a network environment, EMI distorts the signals so that the receiving devices have difficulty interpreting them.
EMI does not always come from expected sources, such as cellular phones. Other types of electric equipment can emit a silent, invisible electromagnetic field that can extend for more than a mile.
There are many sources of EMI:
Any source designed to generate electromagnetic energy
Man-made sources like power lines or motors
Natural events such as electrical storms, or solar and interstellar radiations
Wireless networks are affected by radio frequency interference (RFI). RFI is caused by radio transmitters and other devices transmitting in the same frequency. For example, a cordless telephone can cause problems with a wireless network when both devices use the same frequency. Microwaves can also cause interference when positioned in close proximity to wireless networking devices.
Climate
Climate affects computer equipment in a variety of ways:
If the environment temperature is very high, equipment can overheat.
If the humidity level is very low, the chance of ESD increases.
If the humidity level is very high, equipment can suffer from moisture damage.
Power Fluctuation Types (2.1.2.2)
Voltage is a measure of energy required to move a charge from one location to another. The movement of electrons is called current. Computer circuits need voltage and current to operate electronic components. When the voltage in a computer is not accurate or steady, computer components might not operate correctly. Unsteady voltages are called power fluctuations.
The following types of AC power fluctuations can cause data loss or hardware failure:
Blackout—Complete loss of AC power. A blown fuse, damaged transformer, or downed power line can cause a blackout.
Brownout—Reduced voltage level of AC power that lasts for a period of time. Brownouts occur when the power line voltage drops below 80 percent of the normal voltage level and when electrical circuits are overloaded.
Noise—Interference from generators and lightning. Noise results in poor quality power, which can cause errors in a computer system.
Spike—Sudden increase in voltage that lasts for a short period and exceeds 100 percent of the normal voltage on a line. Spikes can be caused by lightning strikes, but can also occur when the electrical system comes back on after a blackout.
Power surge—Dramatic increase in voltage above the normal flow of electrical current. A power surge lasts for a few nanoseconds, or one billionth of a second.
Power Protection Devices (2.1.2.3)
To help shield against power fluctuation problems, use devices to protect the data and computer equipment:
Surge suppressor—Helps protect against damage from surges and spikes. A surge suppressor diverts extra electrical voltage that is on the line to the ground.
Uninterruptible power supply (UPS)—Helps protect against potential electrical power problems by supplying a consistent level of electrical power to a computer or other device. The battery is constantly recharging while the UPS is in use. The UPS provides a consistent quality of power when brownouts and blackouts occur. Many UPS devices can communicate directly with the computer operating system. This communication allows the UPS to safely shut down the computer and save data prior to the UPS losing all battery power.
Standby power supply (SPS)—Helps protect against potential electrical power problems by providing a backup battery to supply power when the incoming voltage drops below the normal level. The battery is on standby during normal operation. When the voltage decreases, the battery provides DC power to a power inverter, which converts it to AC power for the computer. This device is not as reliable as a UPS because of the time it takes to switch over to the battery. If the switching device fails, the battery cannot supply power to the computer.
Figure 2-1 shows examples of devices to shield against power fluctuations.

Figure 2-1 Types of Power Protection Equipment
Procedures to Protect the Environment (2.1.3)
Most computer and peripherals use and contain at least some materials that can be considered toxic to the environment. This section describes tools and procedures that help identify these materials and the steps for proper handling and disposal of the materials.
Safety Data Sheet (2.1.3.1)
Computers and peripherals contain materials that can be harmful to the environment. Hazardous materials are sometimes called toxic waste. These materials can contain high concentrations of heavy metals such as cadmium, lead, or mercury. The regulations for the disposal of hazardous materials vary by state or country. Contact the local recycling or waste removal authorities in your community for information about disposal procedures and services.
A safety data sheet (SDS) used to be known as a material safety and data sheet (MSDS). A safety data sheet is a fact sheet that summarizes information about material identification, including hazardous ingredients that can affect personal health, fire hazards, and first-aid requirements. The SDS contains chemical reactivity and incompatibility information. It also includes protective measures for the safe handling and storage of materials and spill, leak, and disposal procedures.
To determine if a material is classified as hazardous, consult the manufacturer’s SDS. In the United States, the Occupational Safety and Health Administration (OSHA) requires that all hazardous materials be accompanied by an SDS when transferred to a new owner. The SDS information included with products purchased for computer repairs or maintenance can be relevant to computer technicians. OSHA also requires that employees be informed about the materials that they are working with and be provided with material safety information.
The SDS explains how to dispose of potentially hazardous materials in the safest manner. Always check local regulations concerning acceptable disposal methods before disposing of any electronic equipment.
The SDS contains valuable information:
Name of the material
Physical properties of the material
Hazardous ingredients contained in the material
Reactivity data, such as fire and explosion data
Procedures for spills and leaks
Special precautions
Health hazards
Special protection requirements
In the European Union, the regulation Registration, Evaluation, Authorization and restriction of Chemicals (REACH) came into effect on June 1, 2007, replacing various directives and regulations with a single system.
Equipment Disposal (2.1.3.2)
The proper disposal or recycling of hazardous computer components is a global issue. Make sure to follow regulations that govern how to dispose of specific items. Organizations that violate these regulations can be fined or face expensive legal battles. Regulations for the disposal of the items on this page vary from state to state and from country to country. Check your local environmental regulation agency.
Batteries
Batteries often contain rare earth metals that can be harmful to the environment. Batteries from portable computer systems can contain lead, cadmium, lithium, alkaline manganese, and mercury. These metals do not decay and remain in the environment for many years. Mercury is commonly used in the manufacturing of batteries and is extremely toxic and harmful to humans.
Recycling batteries should be a standard practice. All batteries, including lithium-ion, nickel-cadmium, nickel-metal hydride, and lead-acid, are subject to disposal procedures that comply with local environmental regulations.
Monitors
Handle CRT monitors with care. Extremely high voltage can be stored in CRT monitors, even after being disconnected from a power source.
Monitors contain glass, metal, plastics, lead, barium, and rare earth metals. According to the U.S. Environmental Protection Agency (EPA), monitors can contain approximately 4 pounds (1.8 kg) of lead. Monitors must be disposed of in compliance with environmental regulations.
Toner Kits, Cartridges, and Developers
Used printer toner kits and printer cartridges must be disposed of properly in compliance with environmental regulations. They can also be recycled. Some toner cartridge suppliers and manufacturers take empty cartridges for refilling. Some companies specialize in refilling empty cartridges. Kits to refill inkjet printer cartridges are available but are not recommended, because the ink might leak into the printer, causing irreparable damage. Using refilled inkjet cartridges might also void the inkjet printer warranty.
Chemical Solvents and Aerosol Cans
Contact the local sanitation company to learn how and where to dispose of the chemicals and solvents used to clean computers. Never dump chemicals or solvents down a sink or dispose of them in a drain that connects to public sewers.
The cans or bottles that contain solvents and other cleaning supplies must be handled carefully. Make sure that they are identified and treated as special hazardous waste. For example, some aerosol cans explode when exposed to heat if the contents are not completely used.
Figure 2-2 shows various types of hazardous computer components.

Figure 2-2 Hazardous Computer Components
Proper Use of Tools (2.2)
Using tools properly helps prevent accidents and damage to equipment and people. This section describes and covers the proper use of a variety of hardware, software, and organizational tools specific to working with computers and peripherals.
Hardware Tools (2.2.1)
For every job there is the right tool. Make sure that you are familiar with the correct use of each tool and that the correct tool is used for the current task. Skilled use of tools and software makes the job less difficult and ensures that tasks are performed properly and safely.
General Tool Use (2.2.1.1)
Computer repair requires some task-specific tools. Make sure that you are familiar with the correct use of each tool and that the correct tool is used for the task. Skilled use of tools and software makes the job less difficult and ensures that tasks are performed properly and safely.
A toolkit should contain all the tools necessary to complete hardware repairs. Figure 2-3 shows an example of a PC repair toolkit.

Figure 2-3 Toolkit
As you gain experience, you learn which tools to have available for different types of jobs. Hardware tools are grouped into four categories:
ESD tools
Hand tools
Cleaning tools
Diagnostic tools
ESD Tools (2.2.1.2)
There are two ESD tools: the antistatic wrist strap and the antistatic mat. The antistatic wrist strap protects computer equipment when grounded to a computer chassis. The antistatic mat protects computer equipment by preventing static electricity from accumulating on the hardware or on the technician. Figures 2-4 and 2-5 show the two types of ESD tools discussed above.

Figure 2-4 Antistatic Wrist Strap

Figure 2-5 Antistatic Mat
Hand Tools (2.2.1.3)
Most tools used in the computer assembly process are small hand tools. They are available individually or as part of a computer repair toolkit. Toolkits range widely in size, quality, and price.
Cable Tools (2.2.1.4)
Tools for repairing and creating cables are also part of a computer repair toolkit. Figures 2-6 and 2-7 provide images of common cable tools.

Figure 2-6 Crimper

Figure 2-7 Punch Down Tool
Cleaning Tools (2.2.1.5)
Having the appropriate cleaning tools is essential when maintaining and repairing computers. Using the appropriate cleaning tools such as lint-free cloth, compressed air, cable ties, a parts organizer for small parts helps ensure that computer components are not damaged during cleaning.
Diagnostic Tools (2.2.1.6)
Diagnostic tools are used to test and diagnose equipment.
Digital Multimeter
A digital multimeter, as shown in Figure 2-8, is a device that can take many types of measurements. It tests the integrity of circuits and the quality of electricity in computer components. A digital multimeter displays the information on an LCD or LED screen.

Figure 2-8 Digital Multimeter
Loopback Adapter
A loopback adapter, also called a loopback plug, tests the basic functionality of computer ports. The adapter is specific to the port that you want to test.
Tone Generator and Probe
The tone generator and probe, as shown in Figure 2-9, is a two-part tool. The tone part is connected to a cable at one end using specific adapters. The tone generates a tone that travels the length of the cable. The probe traces the cable. When the probe is in near proximity to the cable to which the tone is attached, the tone can be heard through a speaker in the probe.

Figure 2-9 Tone Generator and Probe
WiFi Analyzer
WiFi analyzers are mobile tools for auditing and troubleshooting wireless networks. Many WiFi analyzers are robust tools designed for enterprise network planning, security, compliance, and maintenance. But WiFi analyzers can also be used for smaller, wireless LANs. Technicians can see all available wireless networks in a given area, determine signal strengths, and position access points to adjust wireless coverage.
Some WiFi analyzers can help troubleshoot a wireless network by detecting misconfigurations, access point failures, and RFI problems.
External Hard Drive Enclosure
Although an external hard drive enclosure is not a diagnostic tool, it is often used when diagnosing and repairing computers. The customer hard drive is placed into the external enclosure for inspection, diagnosis, and repair using a known-working computer. Backups can also be recorded to a drive in an external enclosure to prevent data corruption during a computer repair.
Software Tools (2.2.2)
Software tools help diagnose computer and network problems and determine which computer device is not functioning correctly. A technician must be able to use a range of software tools to diagnose problems, maintain hardware, and protect the data stored on a computer.
Disk Management Tools (2.2.2.1)
You must be able to identify which software to use in different situations. Disk management tools help detect and correct disk errors, prepare a disk for data storage, and remove unwanted files:
Disk Management—Initializes disks, creates partitions, and formats partitions.
Format—Prepares a hard drive to store information.
Scandisk or CHKDSK—Checks the integrity of files and folders on a hard drive by scanning the file system. These tools might also check the disk surface for physical errors.
Optimize Drives—Previously known as Defrag, optimizes space on a hard drive to allow faster access to programs and data.
Disk Cleanup—Clears space on a hard drive by searching for files that can be safely deleted.
System File Checker (SFC)—Scans the operating system’s critical files and replaces files that are corrupt. Use the Windows 8 boot disk for troubleshooting and repairing corrupted files. The Windows 8 boot disk repairs Windows system files, restores damaged or lost files, and reinstalls the operating system. Third-party software tools are also available to assist in troubleshooting problems.
Protection Software Tools (2.2.2.2)
Each year, viruses, spyware, and other types of malicious attacks infect millions of computers. These attacks can damage operating systems, applications, and data. Computers that have been infected may even have problems with hardware performance or component failure.
To protect data and the integrity of the operating system and hardware, use software designed to guard against attacks and to remove malicious programs.
Various types of software protect hardware and data:
Windows Action Center—Checks the status of essential security settings. The Action Center continuously checks to make sure that the software firewall and antivirus programs are running. It also ensures that updates download and install automatically.
Windows Defender—Protects against viruses and spyware.
Window Firewall—Runs continuously to protect against unauthorized communications to and from your computer.
Organizational Tools (2.2.3)
Keeping accurate records and journals during a busy workday can be challenging. Many organizational tools, such as work-order systems, can help the technician document their work.
Reference Tools (2.2.3.1)
Good customer service includes providing the customer with a detailed description of the problem and the solution. It is important that a technician document all services and repairs and that this documentation is available to all other technicians. The documentation can then be used as reference material for similar problems.
Personal Reference Tools
Personal reference tools include troubleshooting guides, manufacturer manuals, quick reference guides, and repair journals. In addition to an invoice, a technician keeps a journal of upgrades and repairs:
Notes—Make notes as you go through the troubleshooting and repair process. Refer to these notes to avoid repeating steps and to determine what needs to be done next.
Journal—Include descriptions of the problem, possible solutions that have been tried to correct the problem, and the steps taken to repair the problem. Note any configuration changes made to the equipment and any replacement parts used in the repair. Your journal, along with your notes, can be valuable when you encounter similar situations in the future.
History of repairs—Make a detailed list of problems and repairs, including the date, replacement parts, and customer information. The history allows a technician to determine what work has been performed on a specific computer in the past.
Internet Reference Tools
The Internet is an excellent source of information about specific hardware problems and possible solutions:
Internet search engines
News groups
Manufacturer FAQs
Online computer manuals
Online forums and chat
Technical websites
Miscellaneous Tools (2.2.3.2)
With experience, you will discover many additional items to add to the toolkit; for example, masking tape can be used to label parts that have been removed from a computer when a parts organizer is not available.
A working computer is also a valuable resource to take with you on computer repairs in the field. A working computer can be used to research information, download tools or drivers, and communicate with other technicians.
Figure 2-10 shows the types of computer replacement parts to include in a toolkit. Make sure that the parts are in good working order before you use them. Using known good components to replace possible bad ones in computers helps you quickly determine which component is not working properly.
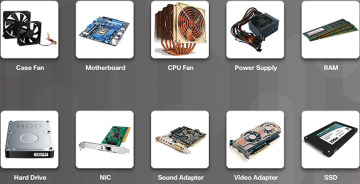
Figure 2-10 Miscellaneous Tools
Demonstrate Proper Tool Use (2.2.4)
This section describes the proper use of common tools used to protect, repair and clean computers and peripherals.
Antistatic Wrist Strap (2.2.4.1)
The antistatic wrist strap is a conductor that connects your body to the equipment that you are working on. When static electricity builds up in your body, the connection made by the wrist strap to the equipment, or ground, channels the electricity through the wire that connects the strap, keeping the charge between you and the equipment equal.
An example of static electricity is the small shock that you receive when you walk across a carpeted room and touch a doorknob. Although the small shock is harmless to you, the same electrical charge passing from you to a computer can damage its components. Wearing an antistatic wrist strap can prevent static electricity damage to computer components.
The wrist strap (seen previously in Figure 2-4) has two parts and is easy to wear:
Step 1. Wrap the strap around your wrist and secure it using the snap or Velcro. The metal on the back of the wrist strap must remain in contact with your skin at all times.
Step 2. Snap the connector on the end of the wire to the wrist strap, and connect the other end either to the equipment or to the same grounding point that the antistatic mat is connected to. The metal skeleton of the case is a good place to connect the wire. When connecting the wire to equipment that you are working on, choose an unpainted metal surface. A painted surface does not conduct electricity as well as unpainted metal.
Antistatic Mat (2.2.4.2)
An antistatic mat is slightly conductive. It works by drawing static electricity away from a component and transferring it safely from equipment to a grounding point:
Step 1. Lay the mat on the workspace next to or under the computer case.
Step 2. Clip the mat to the case to provide a grounded surface on which you can place parts as you remove them from the system.
When you are working at a workbench, ground the workbench and the antistatic floor mat. By standing on the mat and wearing the wrist strap, your body has the same charge as the equipment and reduces the probability of ESD.
Reducing the potential for ESD reduces the likelihood of damage to delicate circuits or components.
Hand Tools (2.2.4.3)
A technician needs to be able to properly use each tool in the toolkit. This page covers many of the various hand tools used when repairing computers.
Screws
Match each screw with the proper screwdriver. Place the tip of the screwdriver on the head of the screw. Turn the screwdriver clockwise to tighten the screw and counter clockwise to loosen the screw.
Screws can become stripped if you do not use the correct size and type of screwdriver. A stripped screw may not tighten firmly or it may not be easily removed. Discard stripped screws.
Flat Head Screwdriver
Use a flat head screwdriver when you are working with a slotted screw. Do not use a flat head screwdriver to remove a Phillips head screw. Never use a screwdriver as a pry bar. If you cannot remove a component, check to see if there is a clip or latch that is securing the component in place.
Phillips Head Screwdriver
Use a Phillips head screwdriver with crosshead screws. Do not use this type of screwdriver to puncture anything. This will damage the head of the screwdriver.
Hex Driver
Use a hex driver to loosen and tighten bolts that have a hexagonal (six-sided) head. Hex bolts should not be over-tightened because the threads of the bolts can be damaged. Do not use a hex driver that is too large for the bolt that you are using.
Component Retrieving Tools
A parts retriever is used to place and retrieve parts that may be hard to reach with your fingers. Do not scratch or hit any components when using these tools.
Various specialty tools, such as Torx bits, antistatic bags and gloves, and integrated circuit pullers, can be used to repair and maintain computers. Always avoid magnetized tools, such as screwdrivers with magnetic heads, or tools that use extension magnets to retrieve small metal objects that are out of reach. Additionally, there are specialized testing devices used to diagnose computer and cable problems:
Multimeter—A device that measures AC/DC voltage, electric current, and other electrical characteristics.
Power supply tester—A device that checks whether the computer power supply is working properly. A simple power supply tester might just have indicator lights, whereas more advanced versions show the amount of voltage and amperage.
Cable tester—A device that checks for wiring shorts, faults, or wires connected to the wrong pins.
Loopback plug—A device that connects to a computer, switch, or router port to perform a diagnostic procedure called a loopback test. In a loopback test, a signal is transmitted through a circuit and then returned to the sending device to test the integrity of the data transmission.
Cleaning Materials (2.2.4.5)
Keeping computers clean inside and out is a vital part of a maintenance program. Dirt can cause problems with the physical operation of fans, buttons, and other mechanical components. On electrical components, an excessive buildup of dust acts like an insulator and traps the heat. This insulation impairs the ability of heat sinks and cooling fans to keep components cool, causing chips and circuits to overheat and fail.
Computer Cases and Monitors
Clean computer cases and the outside of monitors with a mild cleaning solution on a damp, lint-free cloth. Mix one drop of dishwashing liquid with 4 oz. (118 ml) of water to create the cleaning solution. If water drips inside the case, allow enough time for the liquid to dry before powering on the computer.
When computers are in areas where there is excessive dirt and dust, use an enclosure to prevent much of the dirt from harming the computer. The enclosure should have filters to prevent dirt from entering the enclosure. These filters need to be cleaned or replaced on a regular basis.
LCD Screens
Do not use ammoniated glass cleaners or any other solution on an LCD screen, unless the cleaner is specifically designed for the purpose. Harsh chemicals damage the coating on the screen. Often, there is no glass protecting these screens, so be gentle when cleaning them and do not press firmly on the screen.
Clean dusty components with a can of compressed air. Compressed air does not cause electrostatic buildup on components. Make sure that you are in a well ventilated area before blowing the dust out of the computer. A best practice is to wear an air filter mask to make sure that you do not breathe in the dust particles.
Blow out the dust using short bursts from the can. Never tip the can or use the can upside down because doing so will cause the can to freeze. Do not allow the fan blades to spin from the force of the compressed air. Hold the fan in place. Fan motors can be ruined from spinning when the motor is not turned on.
Component Contacts
Use a lint-free cloth that is slightly moistened with isopropyl alcohol to clean the contacts on components. Do not use rubbing alcohol. Rubbing alcohol contains impurities that can damage contacts. Before reinstallation, use compressed air to blow lint off the contacts.
Keyboards
Clean a desktop keyboard with compressed air and then use a handheld vacuum cleaner with a brush attachment to remove the loose dust.
Mice
Use glass cleaner and a soft cloth to clean the outside of the mouse. Do not spray glass cleaner directly on the mouse. If cleaning a ball mouse, you can remove the ball and clean it with glass cleaner and a soft cloth. Wipe the rollers clean inside the mouse with the same cloth. Do not spray any liquids inside the mouse.
Table 2-1 shows the computer items that you should clean and the cleaning materials to use.
Table 2-1 Memory Modules Computer Cleaning Materials
Computer case and outside of monitor |
Mild cleaning solution and lint-free cloth |
LCD screen |
LCD cleaning solution or distilled water and lint-free cloth |
CRT screen |
Distilled water and lint-free cloth |
Heat sink |
Compressed Air |
RAM |
Isopropyl alcohol and lint-free swab |
Keyboard |
Handheld vacuum cleaner with a brush attachment |
Mouse |
Mild cleaning solution and lint-free cloth |
Video—Computer Disassembly (2.2.4.6)
In this video demonstration, a desktop computer will be disassembled using proper lab procedures and tool use. The CPU and cooling unit are left on the motherboard and the motherboard is left in the case, but all other components are removed from the case. Its shows the steps to dissipate the static electricity by touching bare metal case and wearing an antistatic wrist strip while working in the system. It explains that you need to unplug the computer before disassembly so there is no power to it. The video demonstrates removing the process of removing the power and data cable connections, the power supply, adapter cards, and RAM.
Go to the online course to view this video.
Summary (2.3)
This chapter emphasizes the behavior and processes that a worker should use to help in keeping the workplace a safe and productive environment.
Summary (2.3.1)
You have familiarized yourself in the lab with many of the tools used to build, service, and clean computer and electronic components. You have also learned the importance of organizational tools and how these tools help you work more efficiently. Some of the important concepts to remember from this chapter:
Work in a safe manner to protect users and equipment.
Follow all safety guidelines to prevent injuries to yourself and others.
Know how to protect equipment from ESD damage.
Know about and be able to prevent power issues that can cause equipment damage or data loss.
Know which products and supplies require special disposal procedures.
Familiarize yourself with the SDS for safety issues and disposal restrictions to help protect the environment.
Be able to use the correct tools for the task.
Know how to clean components safely.
Use organizational tools during computer repairs.
Summary of Exercises
This is a summary of the labs and activities associated with this chapter.
Check Your Understanding
You can find the answers to these questions in the appendix, “Answers to ‘Check Your Understanding’ Questions.”
What is an accepted method for cleaning computer components?
Using ammonia to clean the LCD screen
Using glass cleaner on a soft cloth to clean the outside of the mouse
Using a lint-free cloth to remove dust inside the computer case
Using rubbing alcohol to clean component contacts
A technician accidentally spills a cleaning solution on the floor of the workshop. Where would the technician find instructions on how to properly clean up and dispose of the product?
The safety data sheet
The insurance policy of the company
The local hazardous materials team
The regulations provided by the local occupational health and safety administration
Which tool can be used to take resistance and voltage measurements?
Loopback plug
Cable tester
Power supply tester
Multimeter
Which tool would be used to create a partition on a hard drive?
Format
SFC
Disk Management
Defrag
Chkdsk
Which statement describes the term ESD?
It is a type of interference caused by electrical motors.
It is a device that supplies a constant level of electrical power to a computer.
It is a measurement of the current flowing though electrical devices.
It is the sudden discharge of static electricity that can adversely affect a component.
Which tool can protect computer components from the effects of ESD?
SPS
Surge suppressor
Antistatic wrist strap
UPS
Which type of fastener is loosened and tightened with a hex driver?
Six-sided bolt
Torx bolt
Slotted screw
Cross head screw
What safety hazard might occur if a partially filled aerosol can is exposed to excessive heat?
Lead poisoning
Explosion
Lethal voltage potential
Breathing hazard
Which tool would be used to scan Windows critical system files and replace any corrupted files?
Chkdsk
Fdisk
SFC
Defrag
What tool would be used to determine which network port attaches to a specific office jack?
Loopback adapter
Punch down tool
Tone probe
Crimper
Which device can protect computer equipment from brownouts by providing a consistent quality of electrical power?
SPS
Surge suppressor
UPS
AC adapter
A technician should keep a personal _____________where all steps taken to repair a computer problem are noted including any configuration changes made.
Journal
Toolkit
Floppy disk
Software list
What would make it easier for a technician to troubleshoot a problem that has been previously solved by another technician?
Online computer manual
Centralized closed trouble tickets
Personal troubleshooting journal
Online forum of manufacturer
Which two devices commonly affect wireless networks? (Choose two.)
Microwaves
External hard drives
Cordless phones
Incandescent light bulbs
Blu-ray players
Home theaters
What are two safety hazards when dealing with laser printers? (Choose two.)
High voltage
Proprietary power bricks
Unwieldy card cages
Heavy metals
Hot components
What three guidelines should be followed to provide safe conditions when computer equipment is being repaired? (Choose three.)
Do not open the power supply.
Turn off the power to the printer and computer before beginning.
If a screwdriver is unavailable, use a knife with a sharp point to loosen screws.
Do not wear loose jewelry unless it is gold, because gold does not conduct electricity.
Ensure that your ID badge is around your neck and visible.
Have all of your extra parts, screws, meters, and tools beside the chassis ready for use.
Bend your knees when lifting heavy objects.
What is a proper directive for using a can of compressed air to clean a PC?
Spray the CPU cooling fan with the compressed air to verify that the fan blade is spinning freely.
Use a long, steady stream of air from the can.
Do not use compressed air to clean a CPU fan.
Do not spray the compressed air with the can upside down.
 Lab—Diagnostic Software (2.2.2.3)
Lab—Diagnostic Software (2.2.2.3)